Midbar (Raspberry Pi Pico Version)
by Northstrix in Circuits > Raspberry Pi
2137 Views, 4 Favorites, 0 Comments
Midbar (Raspberry Pi Pico Version)
Less than two weeks ago, I released the Midbar V2.5. That version of Midbar was protected from the chosen-plaintext attack, block-swapping attack, and brute force attack. It could discern legitimate ciphertexts from forged ones. It was the second version of Midbar that could verify the integrity of the whole records and the first version of Midbar that utilized the 3DES + AES + Blowfish + Serpent encryption algorithm In CBC Mode.
Perhaps, it was (in my opinion) so good that I've decided to port it to the Raspberry Pi Pico. I didn't call it "Midbar (Raspberry Pi Pico Version) V2.5" because it's missing the SQLite3 RDBMS and doesn't have a secure communication channel. But I wouldn't call it a "watered down" version of the Midbar V2.5 either because, at the very least, it has the vault capability of the Midbar V2.5 intact, handles the PS/2 keyboard much better than the Midbar V2.5 and can easily encrypt and then decrypt a 10000-characters long string using the 3DES + AES + Blowfish + Serpent encryption algorithm In CBC Mode. Anyway, after a long consideration, I've decided to call it the "Midbar (Raspberry Pi Pico Version)."
In case you want to know why I called this project Midbar - Midbar (מדבר) is a Hebrew word that means "pasture," "uninhabited land," "wilderness," "large tracts of wilderness (around cities)," "desert." I had two reasons for choosing the word Midbar as the name of this project. First - while working on my previous projects, I noticed that the so-called "device that keeps your personal data secure in an encrypted form" market is pretty much a "desert around the oasis of the password manager market." Second - I couldn't find a better word to describe that project. At first, I wanted to call it a "Password Vault," but then I realized that it's more than just a password vault. So, I just called it Midbar!
*Edited: After writing this tutorial and publishing the original firmware, I made a version of the firmware that's more stable than the original one. You can find it in the "V1.0s" folder.
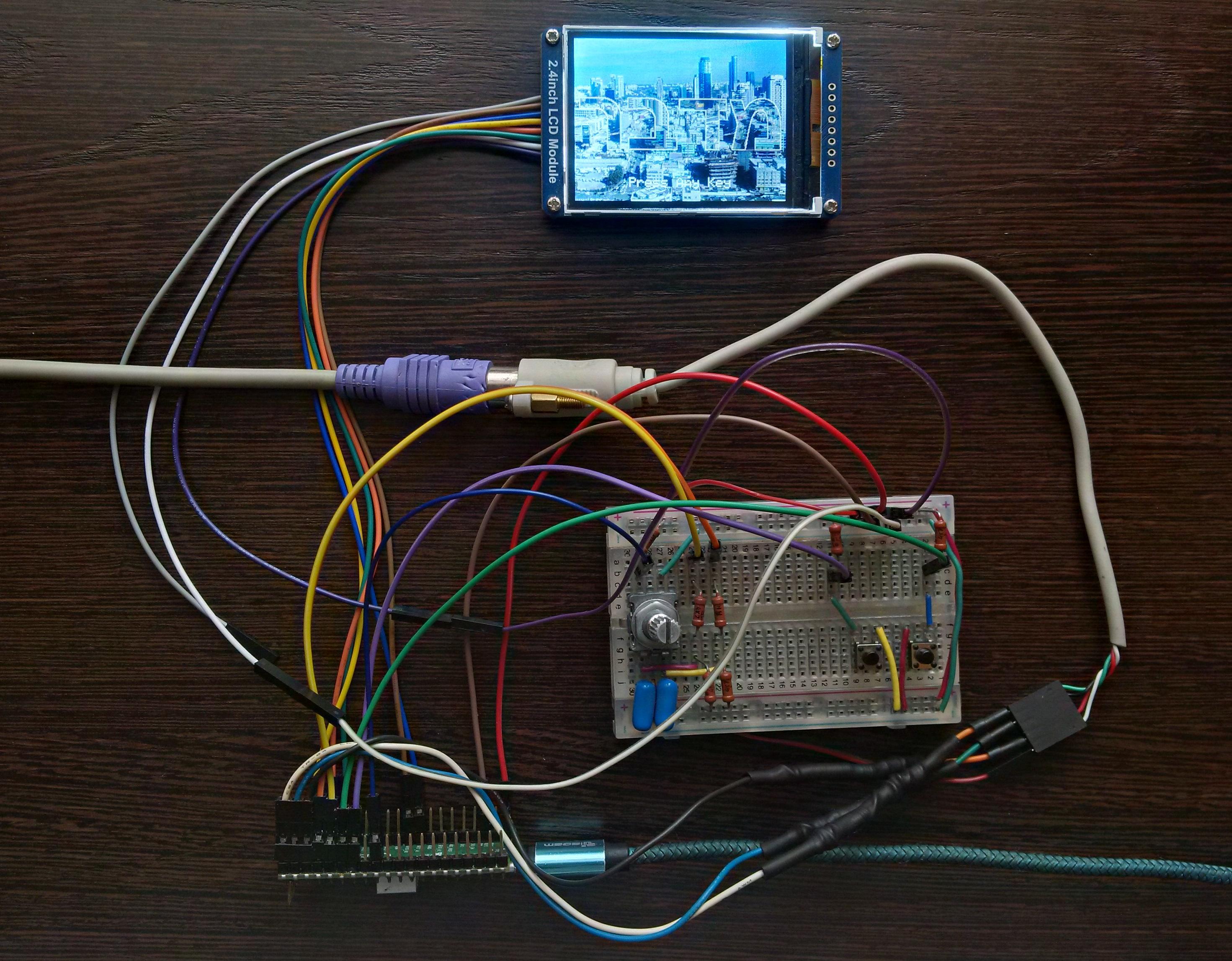
Supplies
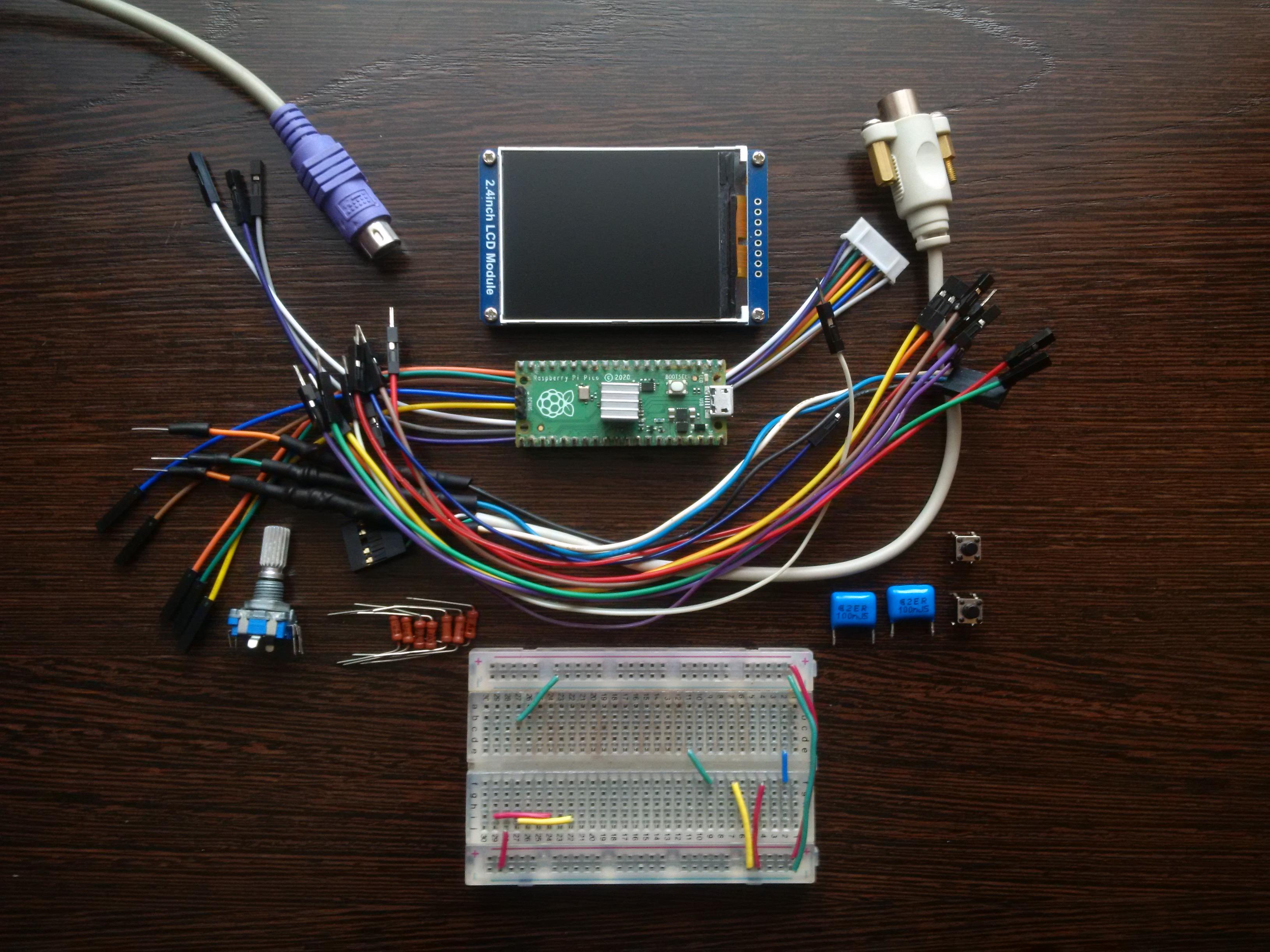
- Raspberry Pi Pico x1
- 2.4 Inch TFT LCD with ILI9341 x1
- EC11 Rotary Encoder x1
- PS/2 Keyboard x1
- PS/2 Port x1
- 4.7k resistors x7
- 100nf capacitors x2
- Buttons x2
3DES + AES + Blowfish + Serpent in CBC Mode
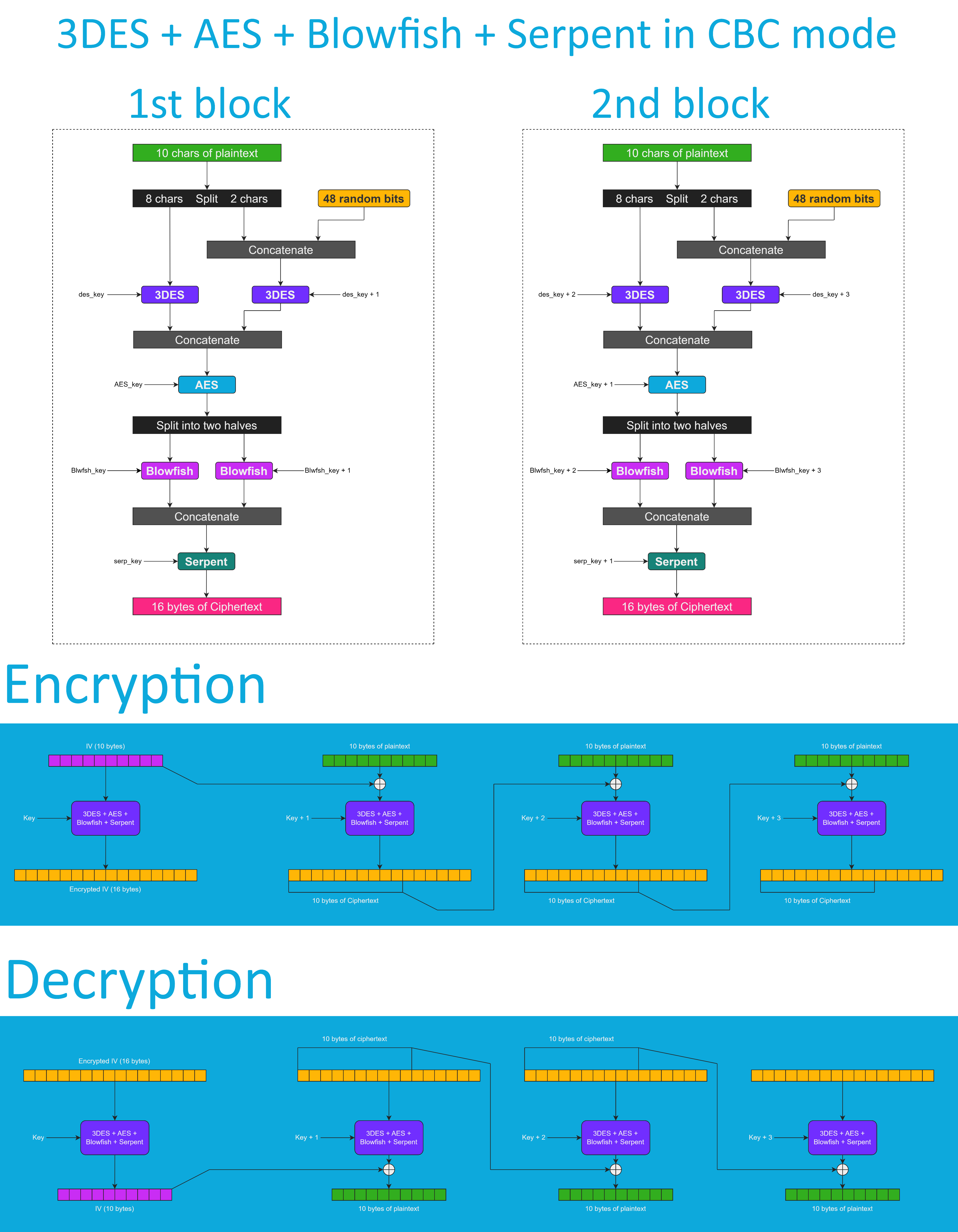
Don't get me wrong - the "3DES + AES + Blowfish + Serpent" encryption algorithm ain't exactly what I would call "cryptographically weak," but operating it in a weird derivation of the ECB mode wasn't the best idea that I had. Although that wouldn't've allowed the attacker to produce the legitimate ciphertext by swapping the blocks within the ciphertext, an attacker could still make a legitimate ciphertext by replacing the nth block of the ciphertext N1 with the nth block of the ciphertext N2. To fix that vulnerability (instead of just notifying the user that the decrypted ciphertext might've been forged), I made the "3DES + AES + Blowfish + Serpent" encryption algorithm work in CBC mode. So, if an attacker replaces a block of ciphertext, it spoils not just that block but also the subsequent one.
I'll be honest with you, the bit-flipping attack "kinda works," but I doubt that it would ever go unnoticed because of the "HMAC-SHA256"-based integrity verification feature.
And by the way, out of all encryption algorithms utilized by this version of Midbar, the "3DES + AES + Blowfish + Serpent" is the only algorithm that works in CBC mode. Beware of it!
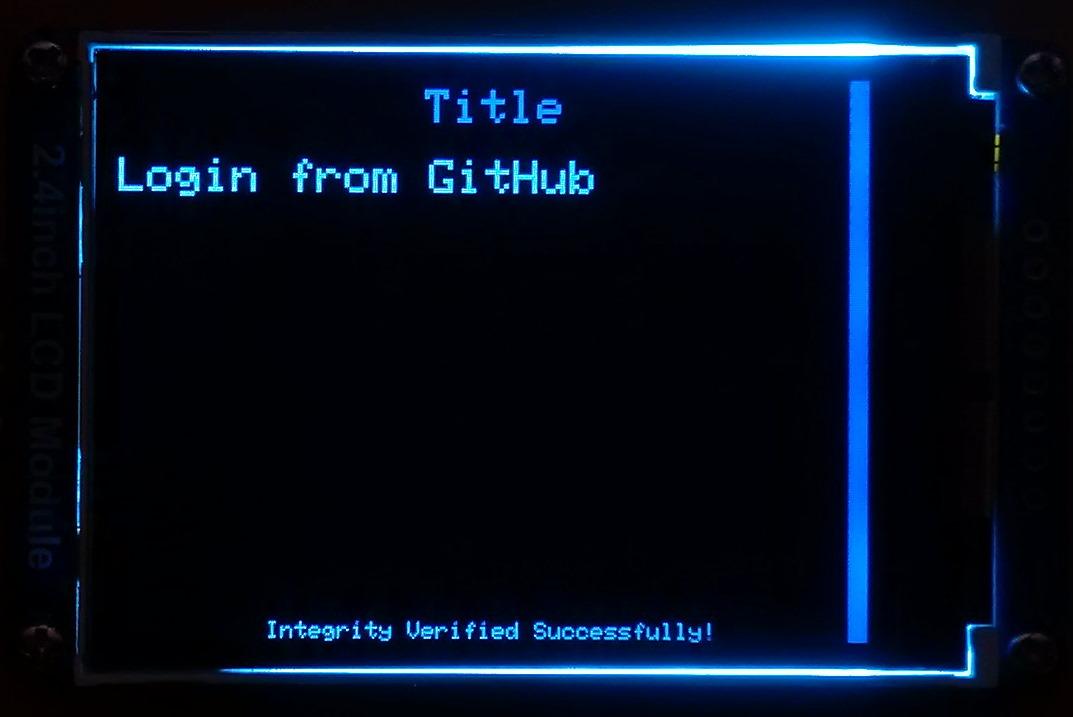
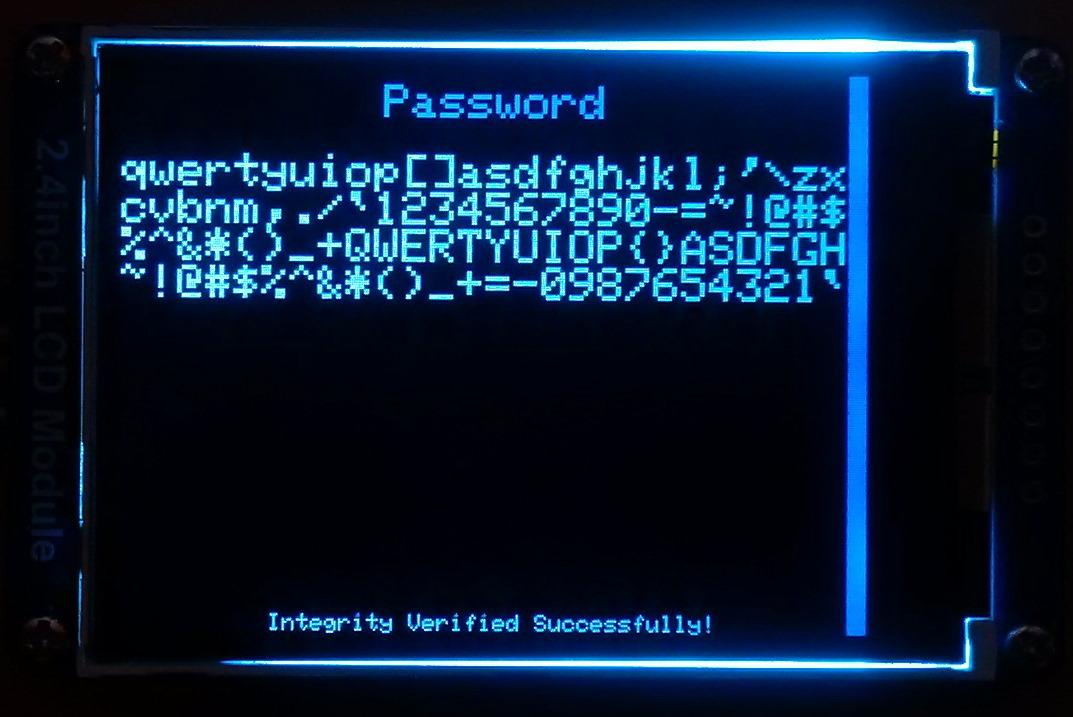
Integrity Verification
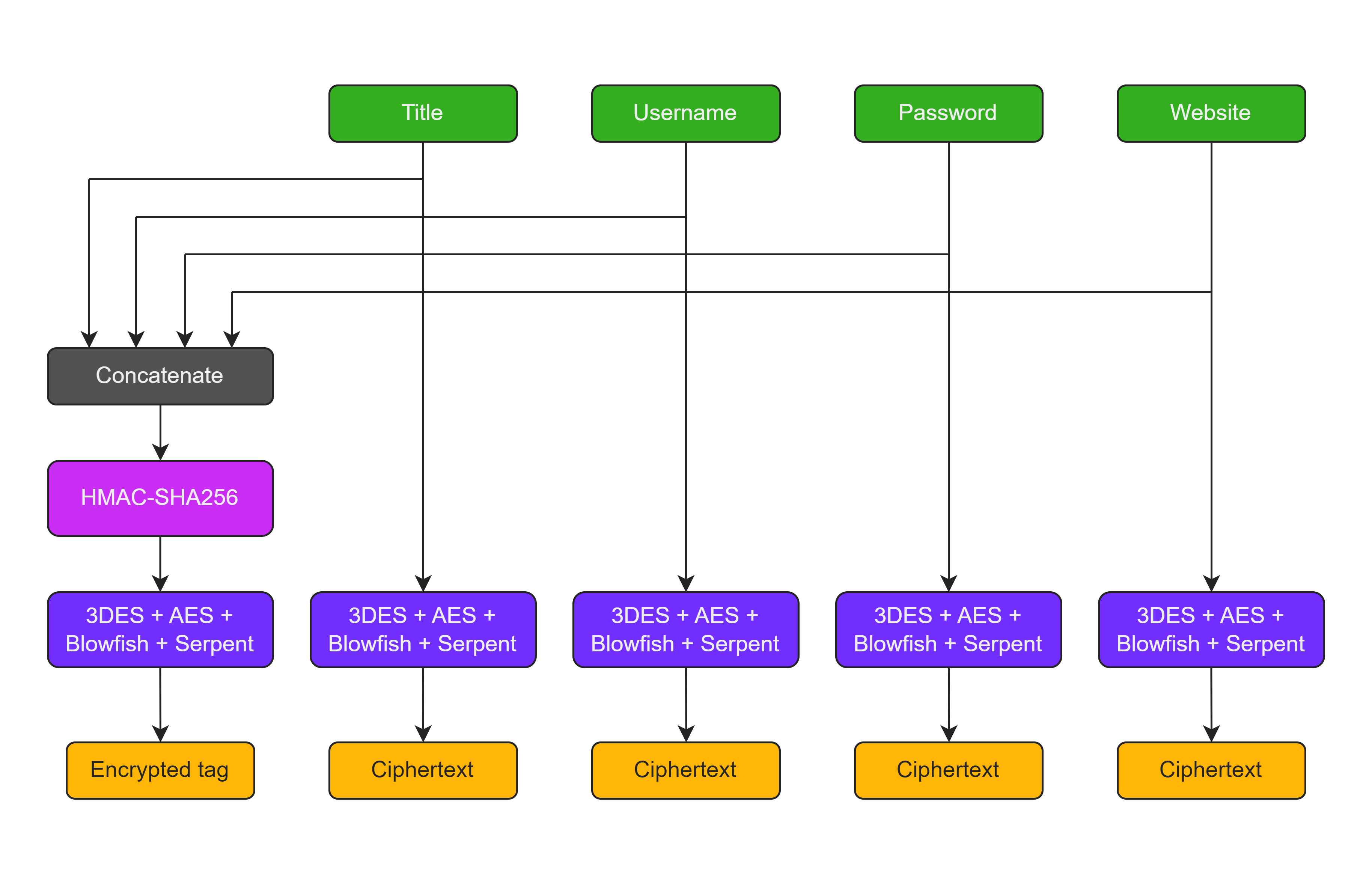
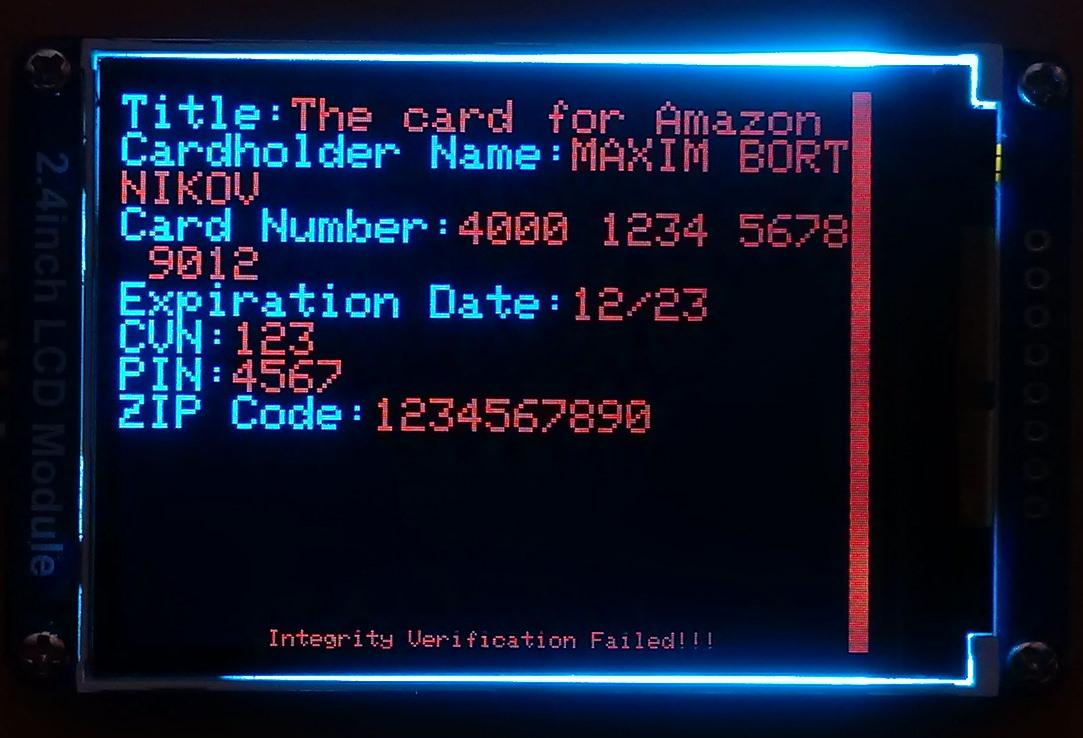
The Midbar (Raspberry Pi Pico Version) is the third version of Midbar that verifies the integrity of the whole record. So, the legitimate ciphertexts moved between the cells aren't much of a threat to it.
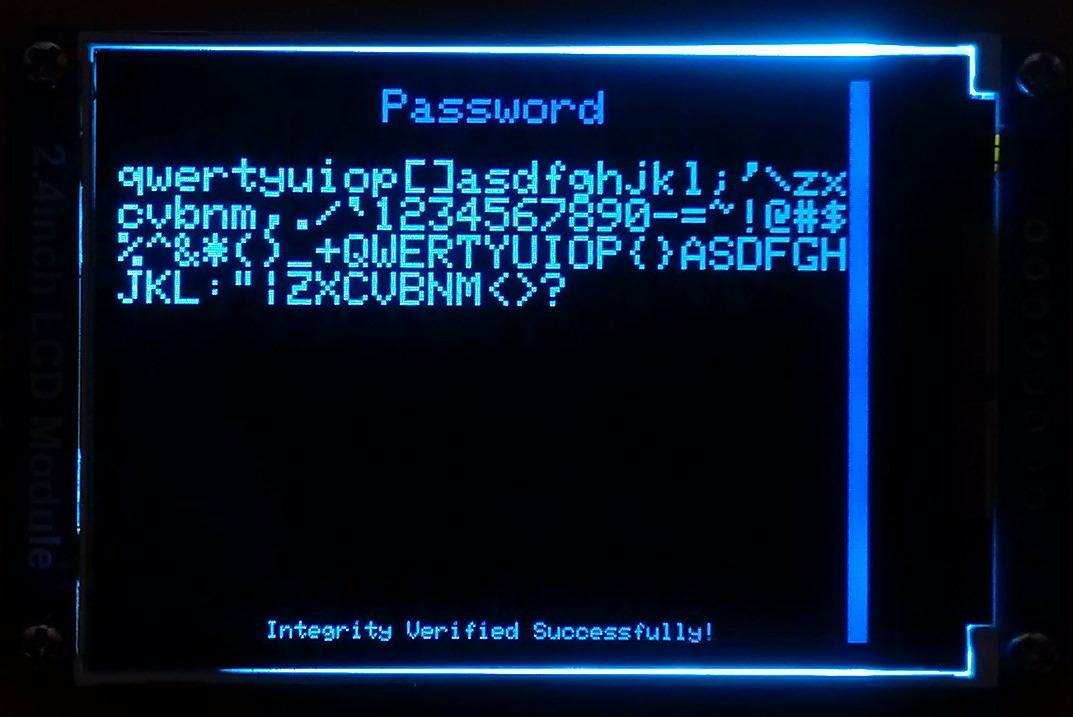
The "HMAC-SHA256"-based integrity verification feature works as follows:
When you add a record to Midbar, it concatenates all the data you've entered into a single string, computes a tag for it, and then stores that tag in the encrypted form.
When Midbar decrypts your data, it also decrypts the previously calculated tag and computes a new tag for the decrypted data. It then compares both tags, and if they don't match - Midbar notifies you that the integrity verification failed.
*All credentials demonstrated here are entirely fictitious. Any similarity to actual credentials is purely coincidental.
Configure Arduino IDE *Optional
If you've never flashed the Raspberry Pi Pico before you need to configure the Arduino IDE first.
Configuring IDE isn't a part of this tutorial. You can read about it here https://www.tomshardware.com/how-to/program-raspberry-pi-pico-with-arduino-ide
Download Firmware
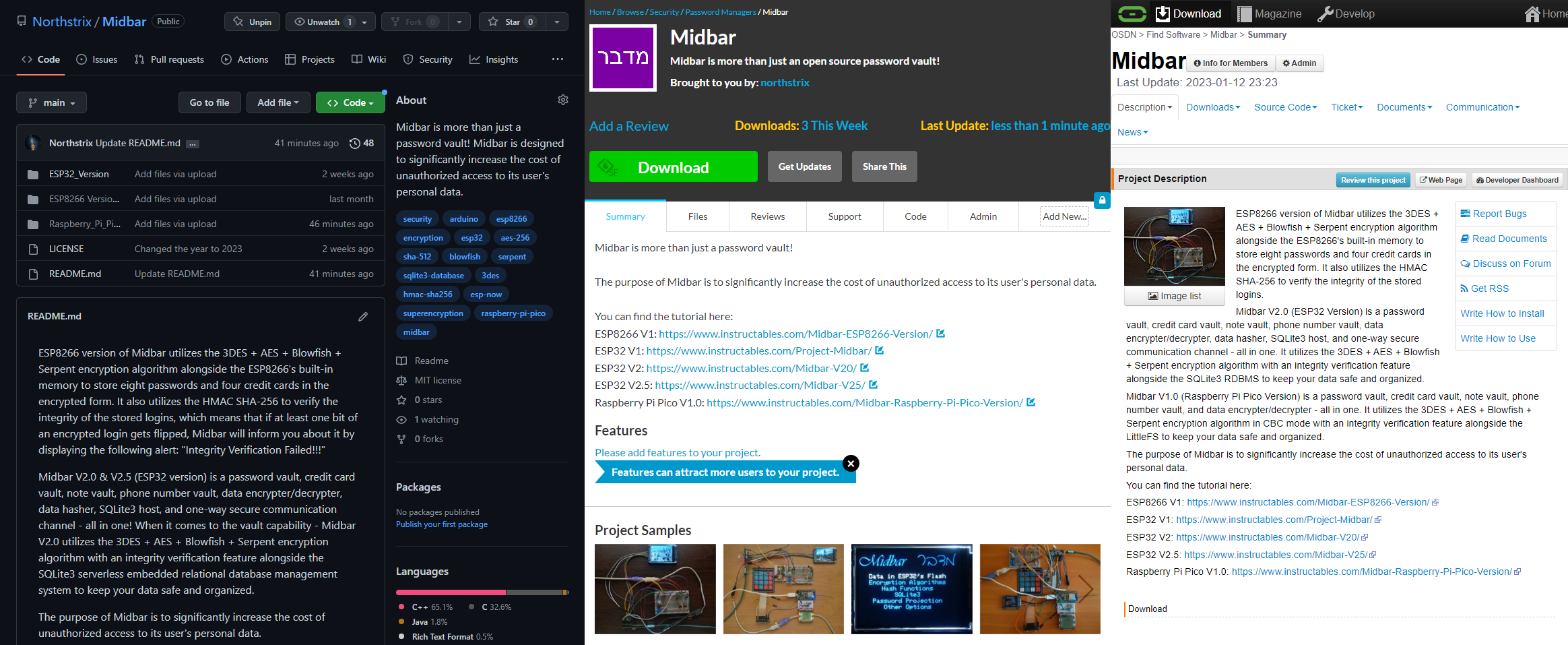
You can download the firmware for Midbar from one of these sources.
SourceForge: https://sourceforge.net/projects/midbar/
OSDN: https://osdn.net/projects/midbar/
GitHub: https://github.com/Northstrix/Midbar
If you just need the firmware for the device alongside the RNG, then I would advise you to download a 0.6 MB archive either from SourceForge or OSDN.
But if you need the firmware for all versions of Midbar alongside the extra code, photos, and diagrams, in that case, I would advise you to download the 84.2 MB archive from GitHub.
Download and Install the Libraries
Arduino_GFX: https://github.com/moononournation/Arduino_GFX
PS2KeyAdvanced: https://github.com/techpaul/PS2KeyAdvanced
EncButton: https://github.com/GyverLibs/EncButton
*Libraries for the "V1.0s:"
Adafruit_ILI9341: https://github.com/adafruit/Adafruit_ILI9341
Adafruit_BusIO: https://github.com/adafruit/Adafruit_BusIO
The process of unpacking libraries is typical. You can unpack the content of the archive into the folder: ...\Arduino\libraries. Or open the Arduino IDE, click to the Sketch -> Include Library -> Add .ZIP Library... and select every archive with libraries.
Other required libraries are already present in one way or another.
Install Arduino-pico-littlefs-plugin
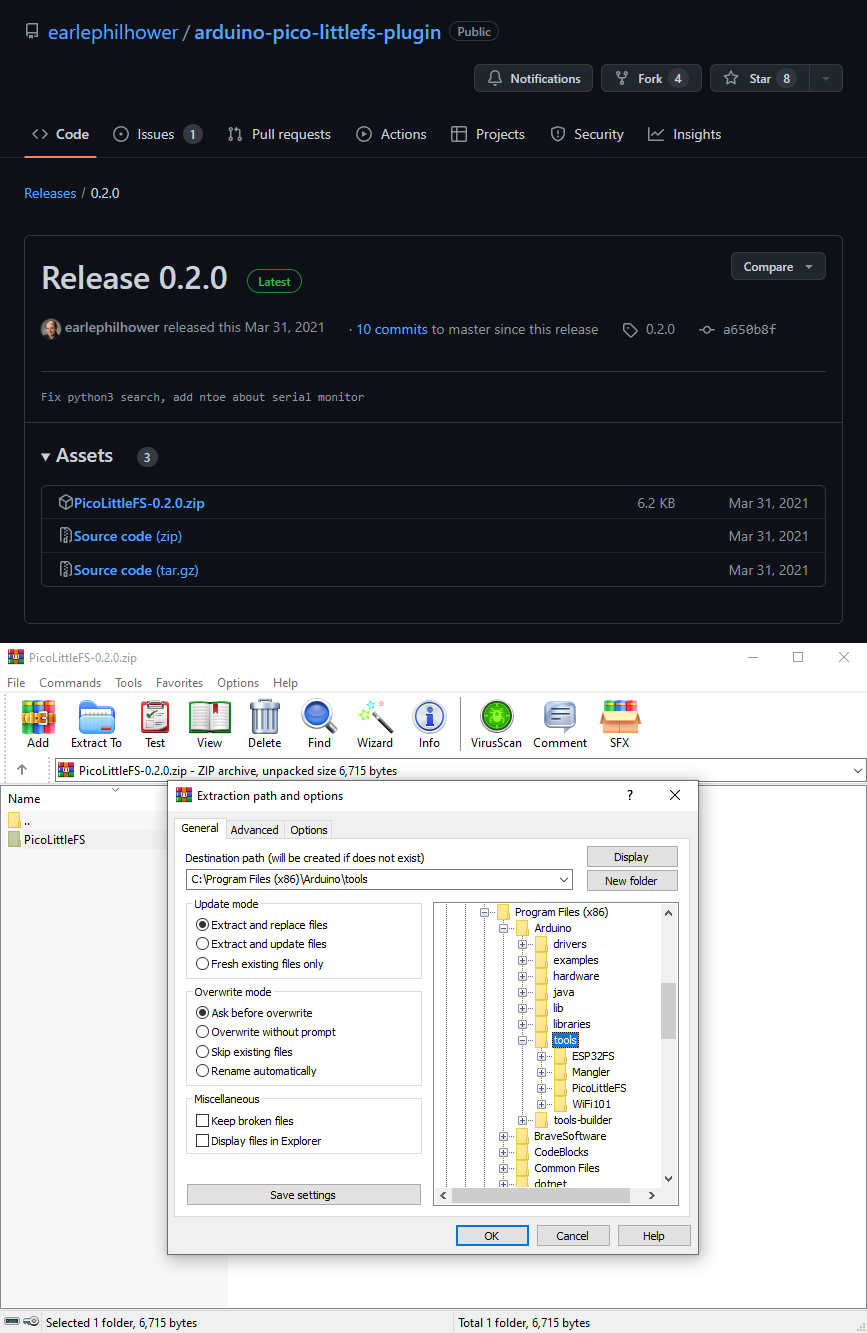
The primary purpose of the arduino-pico-littlefs-plugin is to let you upload the files into the RPI's flash memory. In this tutorial, the purpose of this tool is to format the RPI's flash.
Download the file called PicoLittleFS-0.2.0.zip from https://github.com/earlephilhower/arduino-pico-littlefs-plugin/releases/tag/0.2.0
And then extract the content of the archive into the "...\Arduino\Tools\" folder.
After that, restart the Arduino IDE.
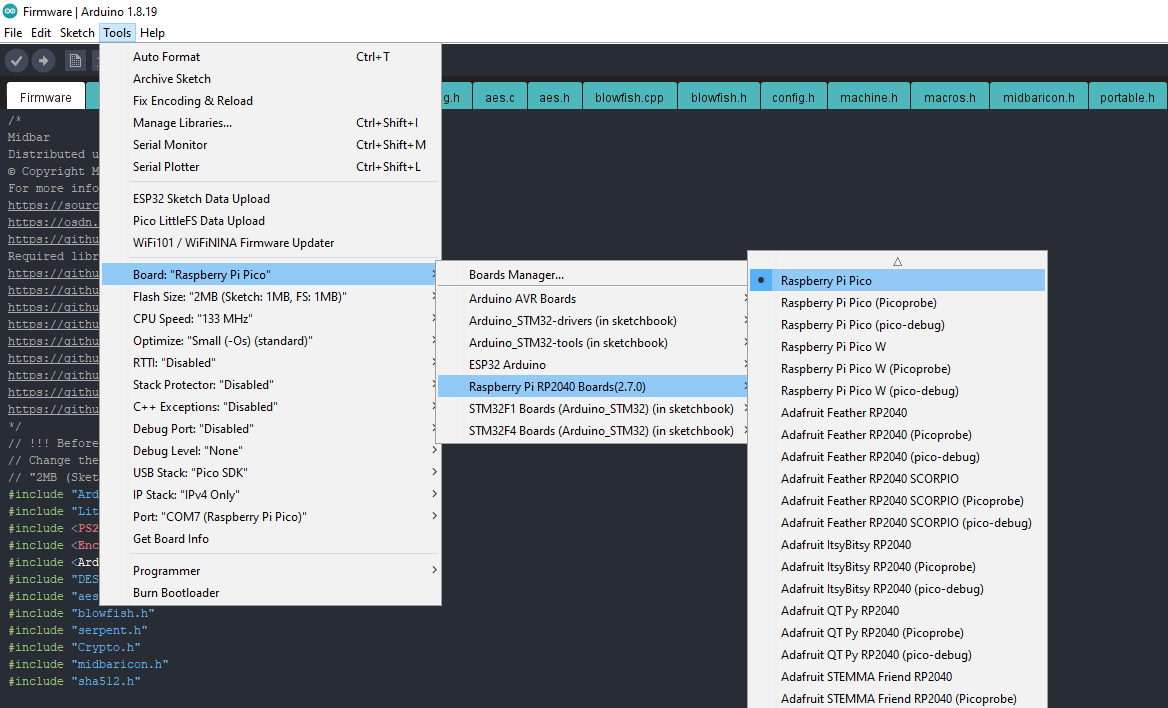
Change the "Flash Size" to the "2MB (Sketch: 1MB, FS: 1MB)"
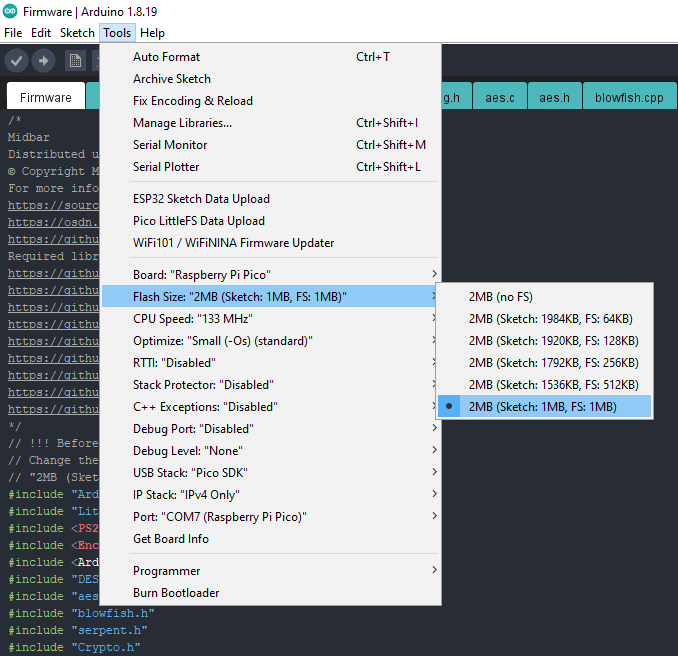
Midbar needs memory allocated for the file system to function.
To allocate the memory for the file system, click "Tools" -> "Flash Size" -> "2MB (Sketch: 1MB, FS: 1MB)"
Format Raspberry Pi Pico's Built-In Flash Memory
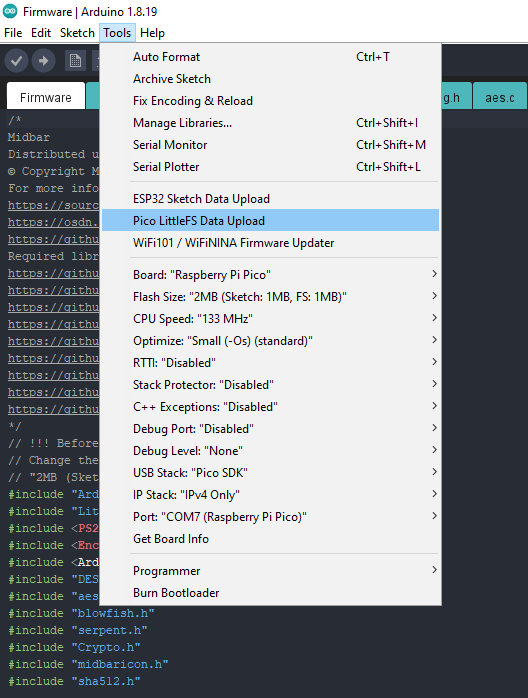
Click "Tools" -> "Pico LittleFS Data Upload." Then click "Yes" in the pop-up window. The program is going to format the RPI's flash memory.
Generate Keys
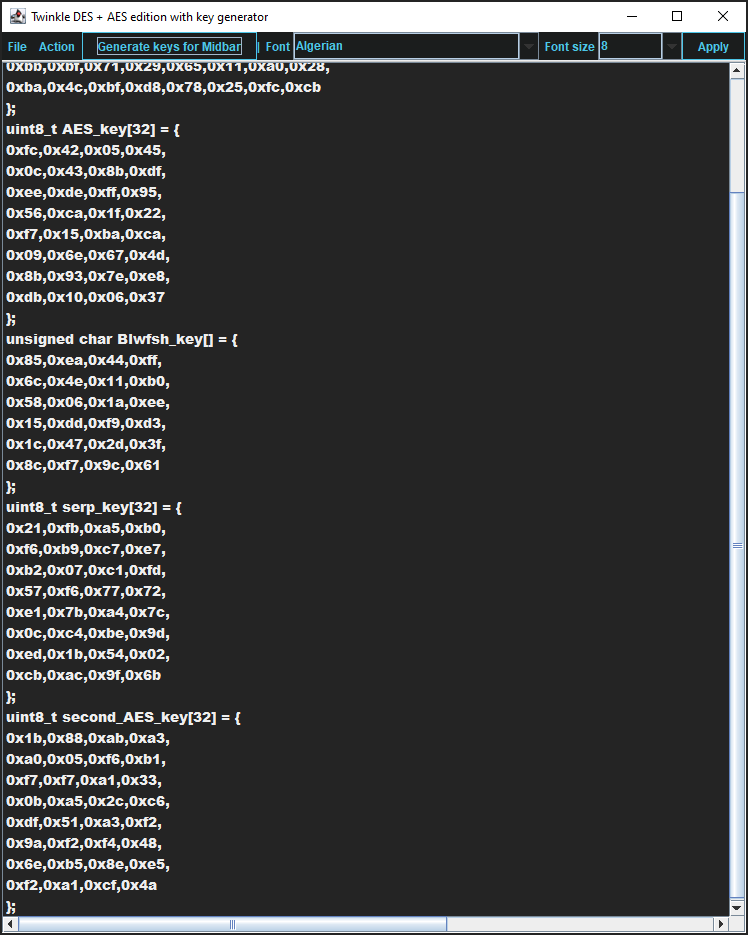
To make the unauthorized deciphering of your data computationally infeasible - It is crucial to generate your own keys and never reuse them
It's entirely up to you how to generate the keys. I can only offer you an option to do so.
I've modified one of my previous projects to work as a random number generator, the generated output seems "random enough" for me, but I haven't run any tests. So, I can't guarantee that it's random.
Use it at your own risk!
To generate the keys - launch gen.exe from the "Raspberry_Pi_Pico_Version\V1.0\Untested RNG" folder and click the "Generate keys for Midbar" button. The background turns from dark gray to light gray when you press that button.
Modify the Firmware
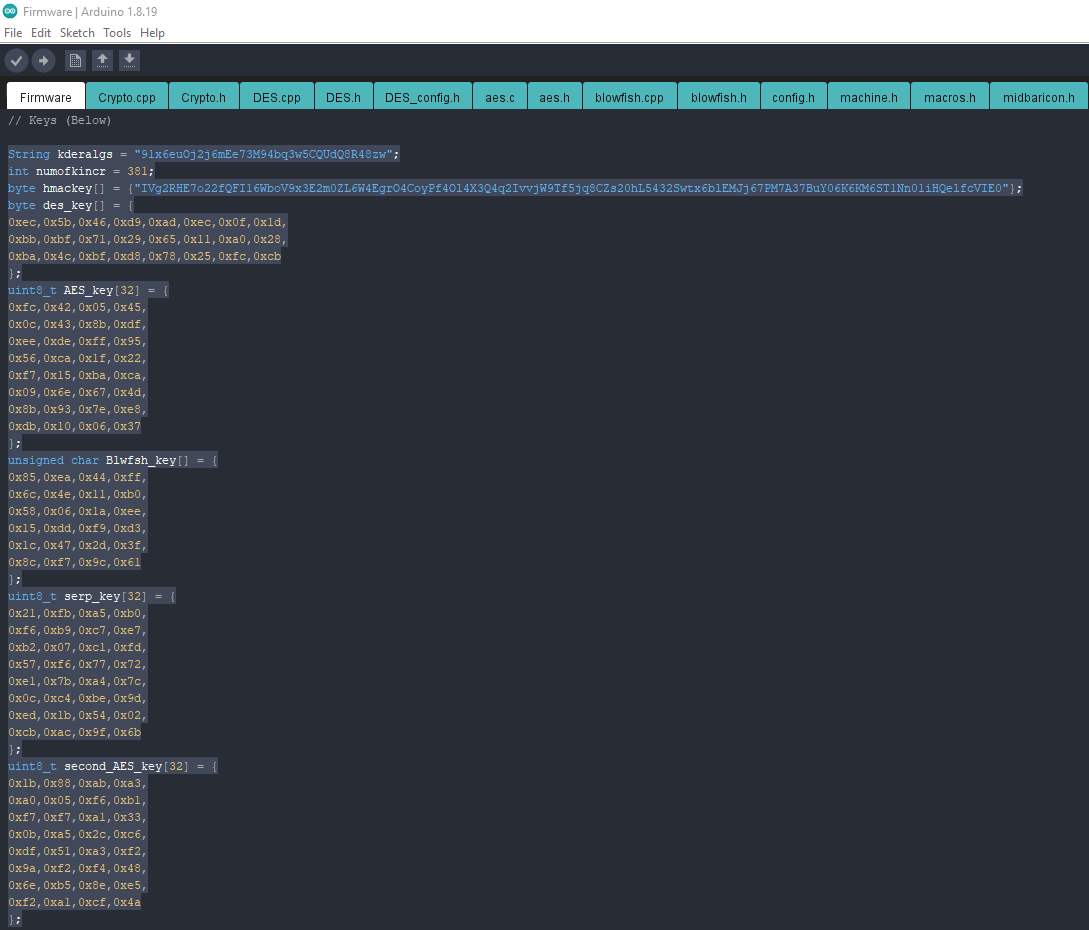
Open the "Firmware.ino" file from the "Raspberry_Pi_Pico_Version\V1.0\Firmware" folder, and then replace my keys with those you've generated.
Flash Raspberry Pi Pico
Upload the firmware from the "Raspberry_Pi_Pico_Version\V1.0\Firmware" folder into the Raspberry Pi Pico.
Assemble the Midbar
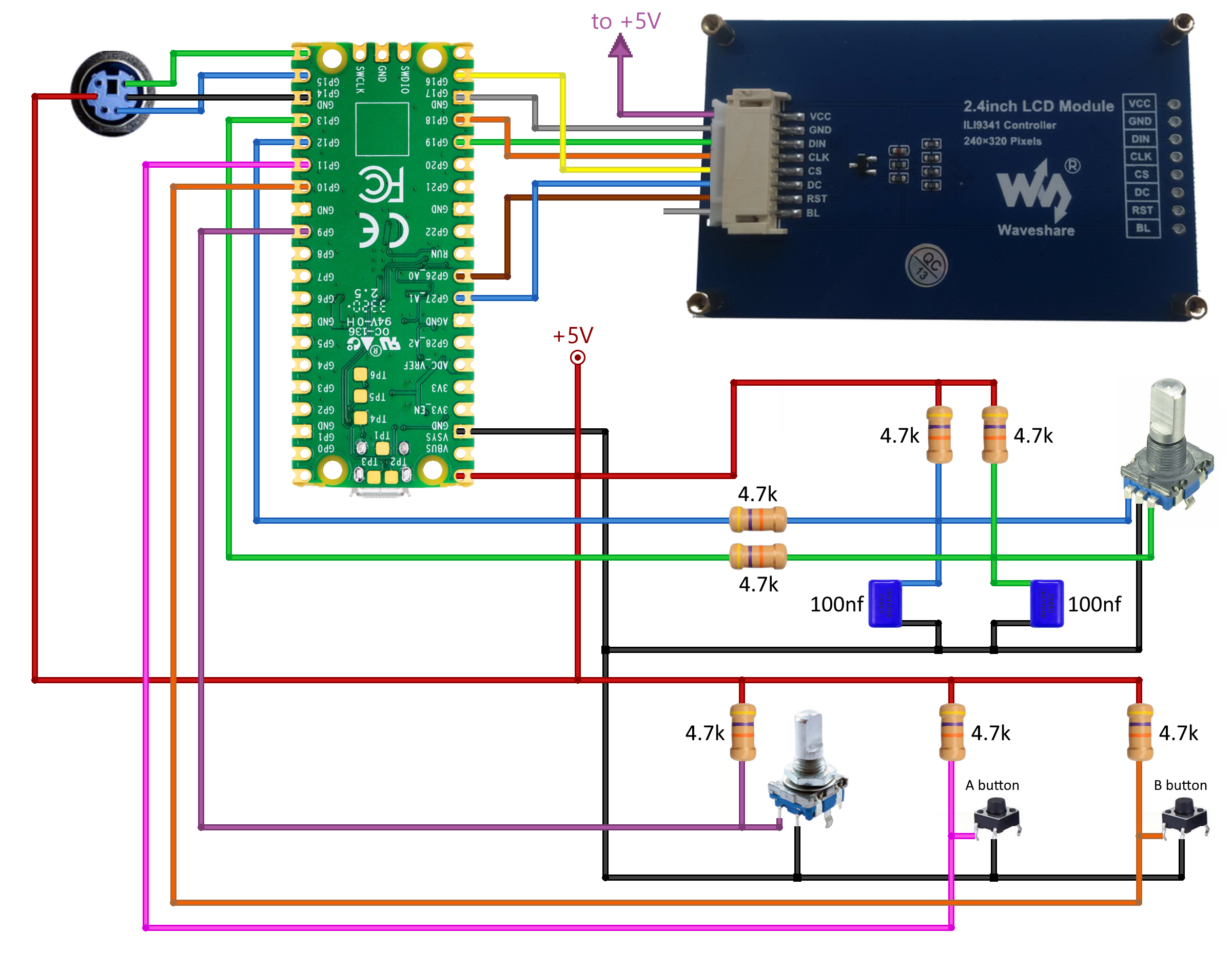
Assembling the Midbar shouldn't be hard. In my opinion, the most tangled part of the process is to connect the encoder with its periphery the right way.
As for the possible component replacements:
- You can replace 4.7k resistors with 4.7k - 10k resistors;
- And you can replace the capacitors with 22nf - 100nf capacitors.
Power the Midbar Up

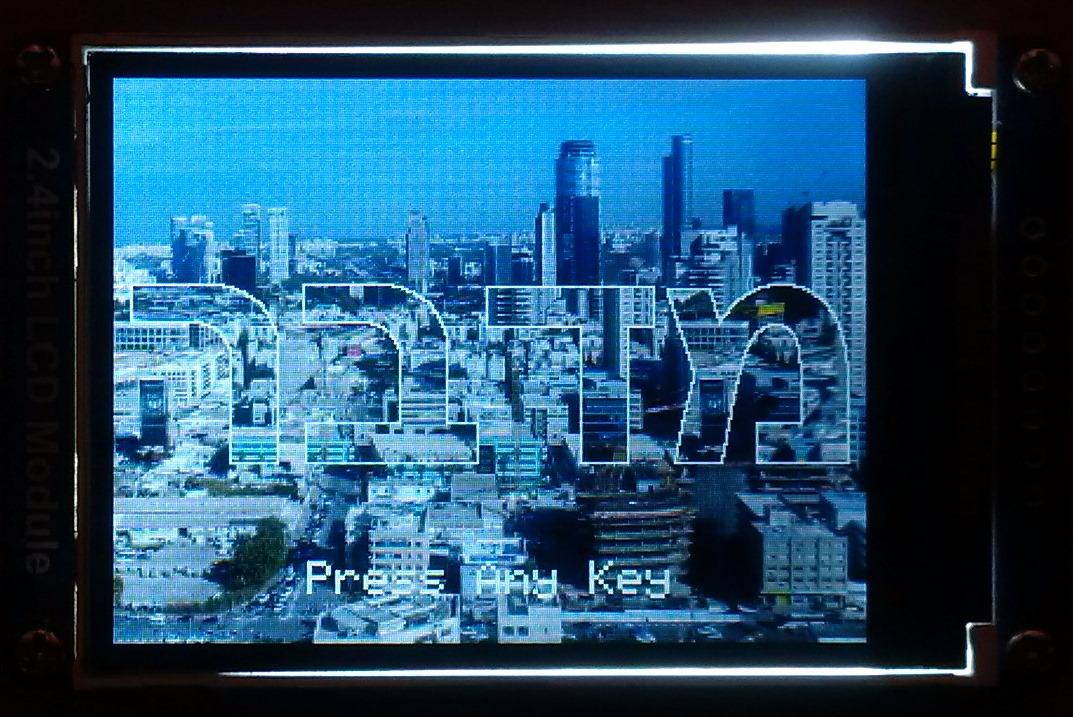
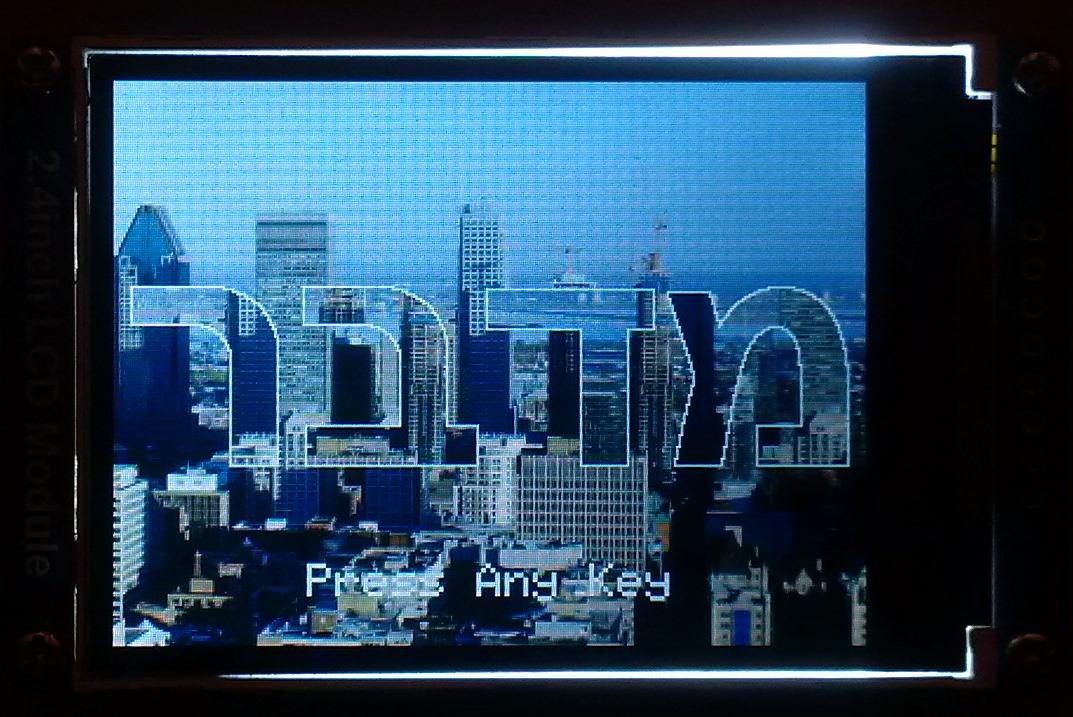
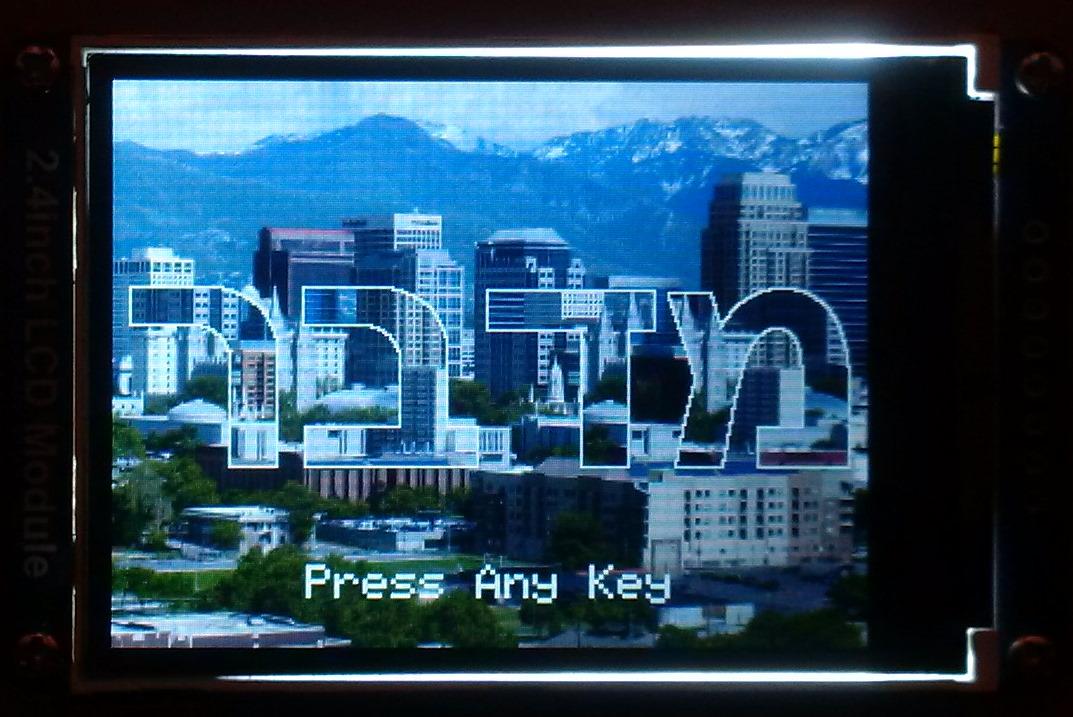
Unlike the previous version of Midbar, which only had one lock screen, that one has four. The lock screen is randomly chosen at startup.
After the Midbar has chosen the lock screen, it displays the word "מדבר" with the shifting background and the "Press Any Key" inscription.
At that point, press any key to get to the next tab.
*Credit for photos:
Image by RobinSaville from Pixabay
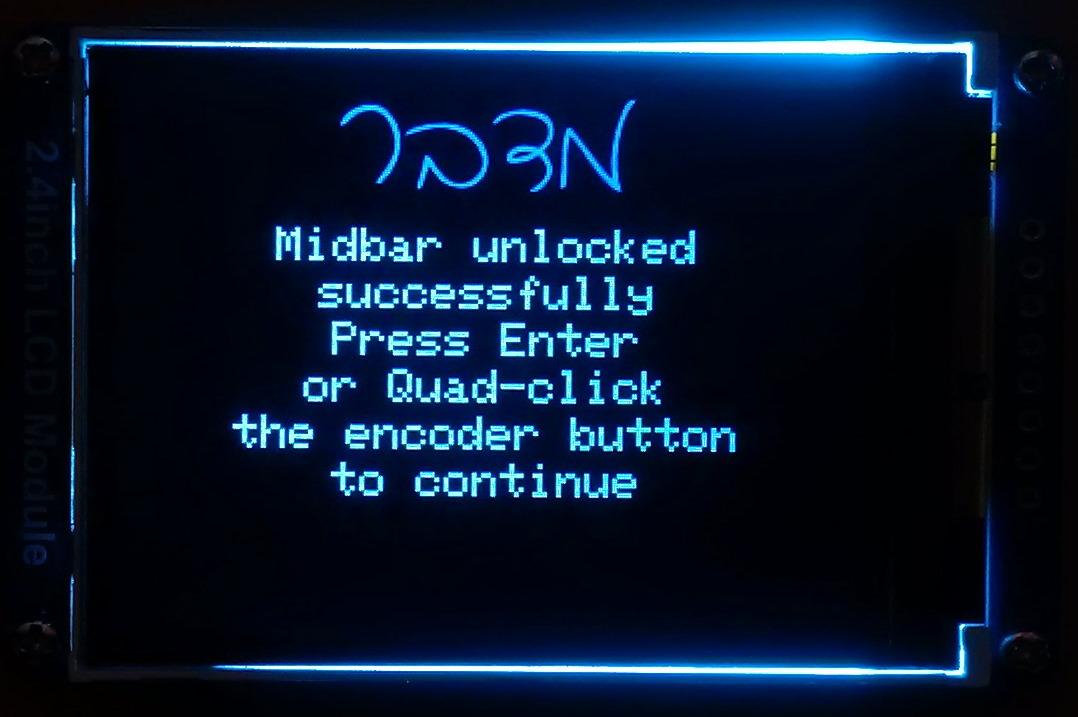
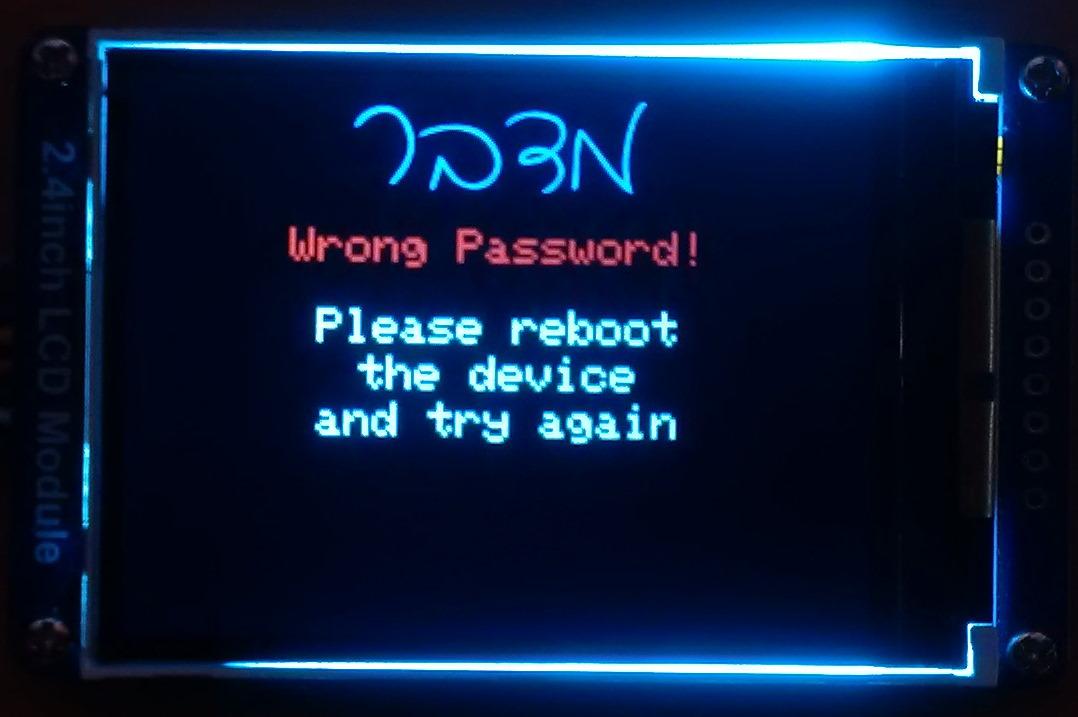
Set the Master Password
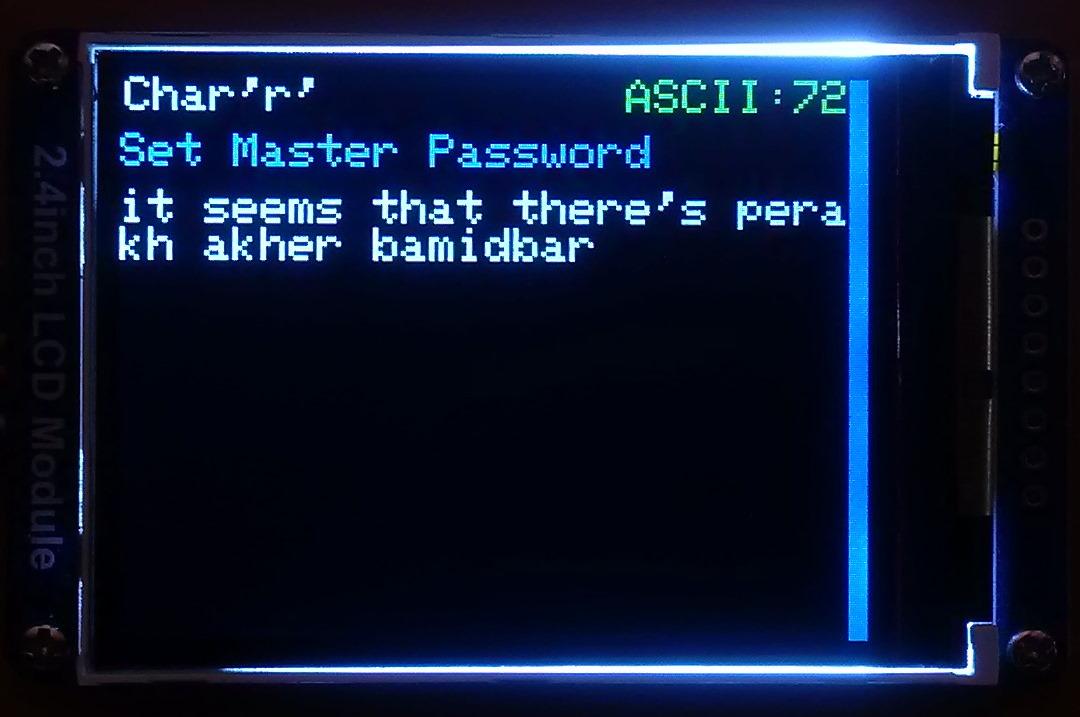
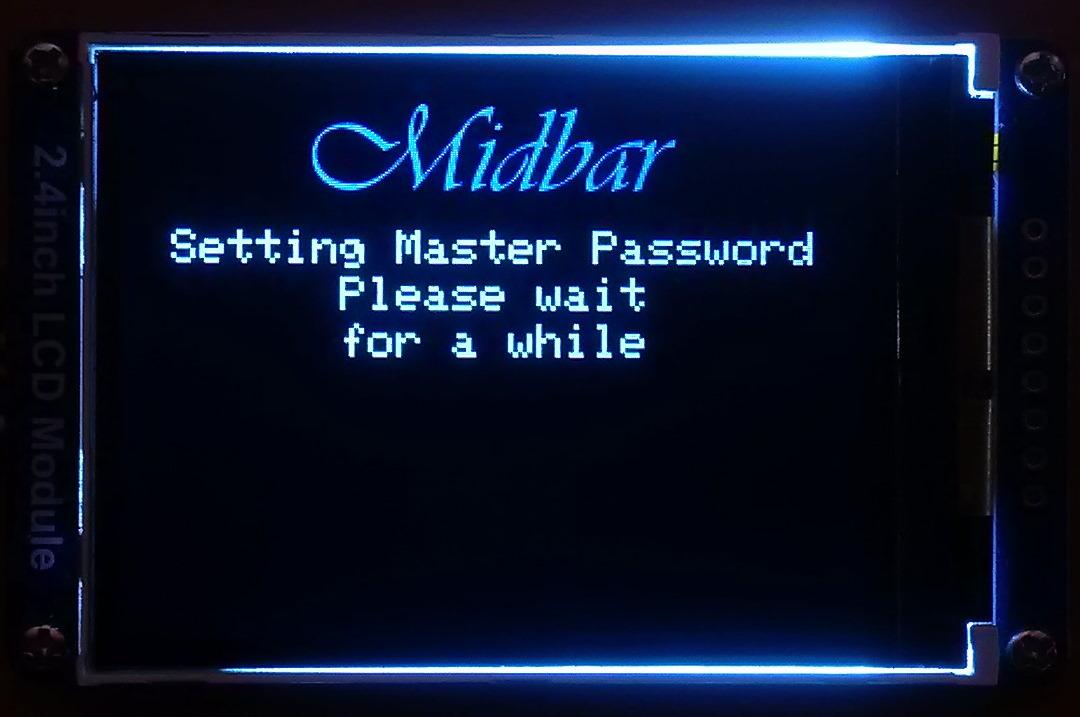
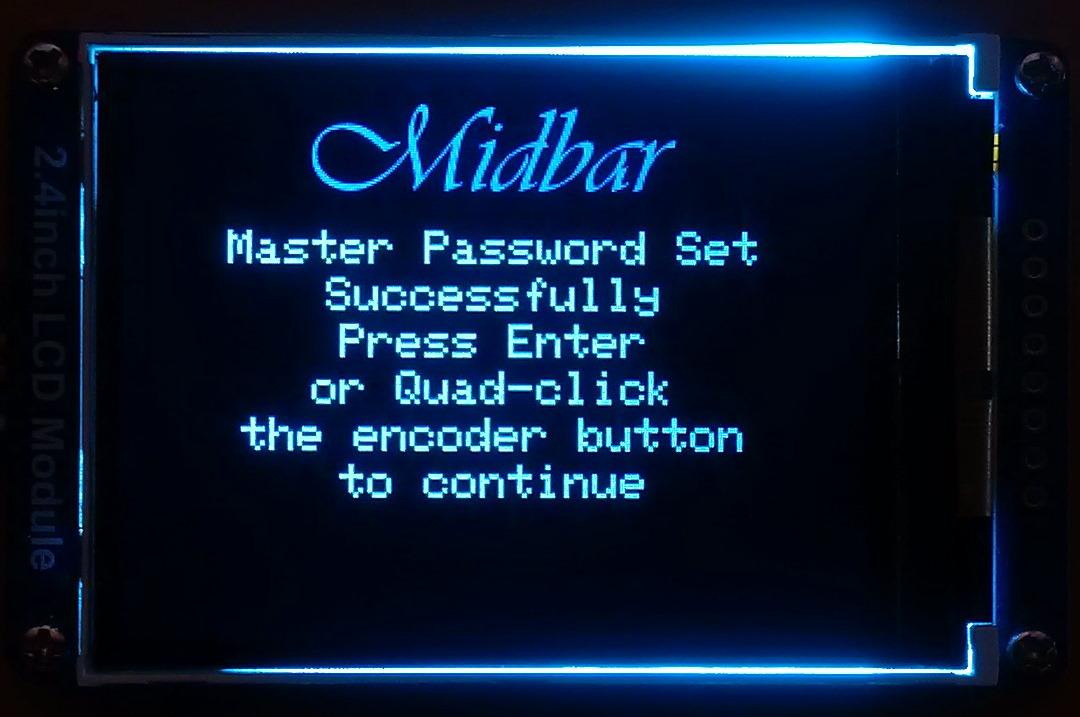
To use the Midbar, you first need to set the master password.
You can only enter the master password using the encoder and PS/2 keyboard.
And remember that you can't change your master password without performing the factory reset first!
Midbar won't be able to decrypt your data without your master password because the keys for the encryption algorithms are partially derived from it. Perhaps, it won't even unlock without the correct master password.
When you're done entering your master password, either quad-click the encoder button or press the "Enter" on the PS/2 keyboard.
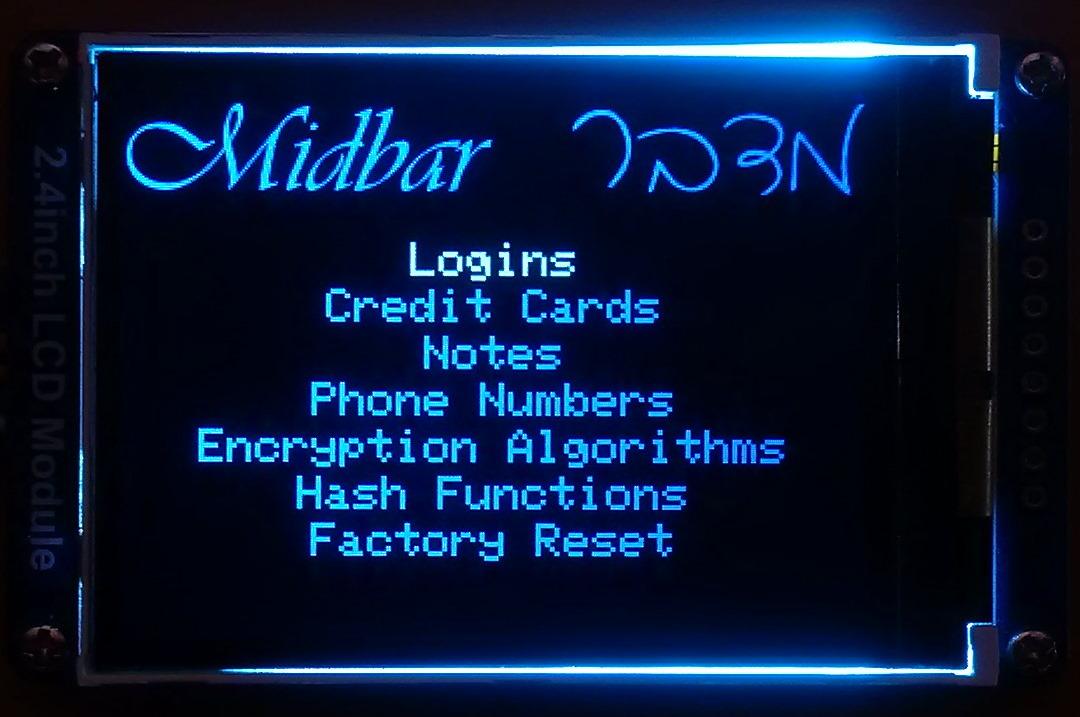
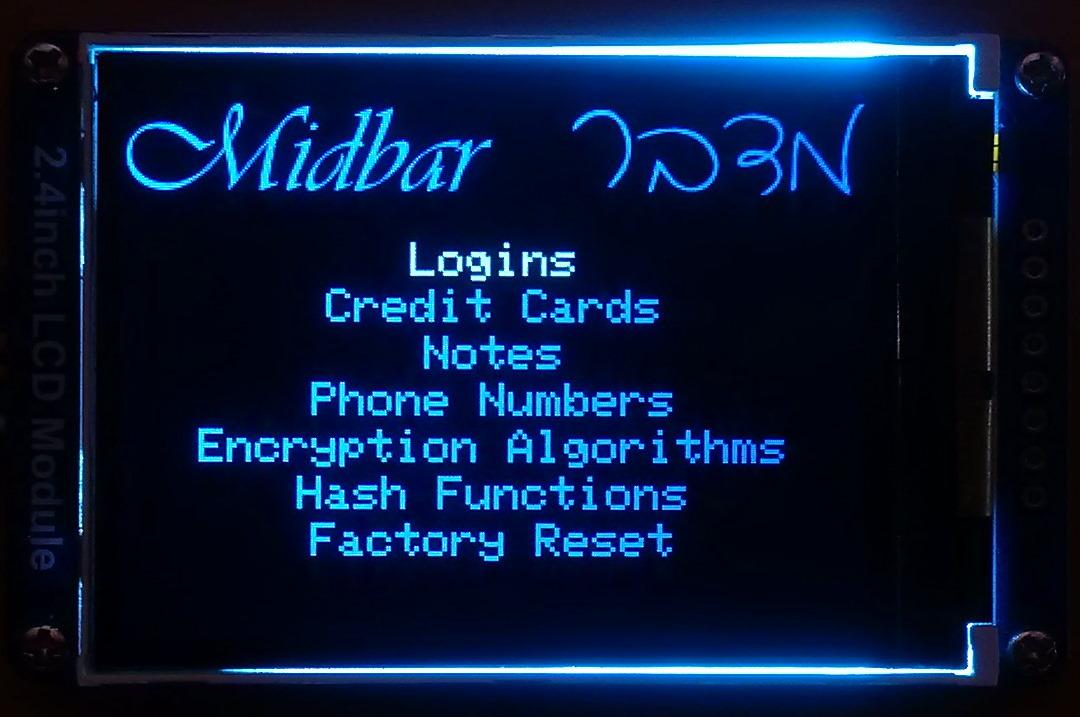
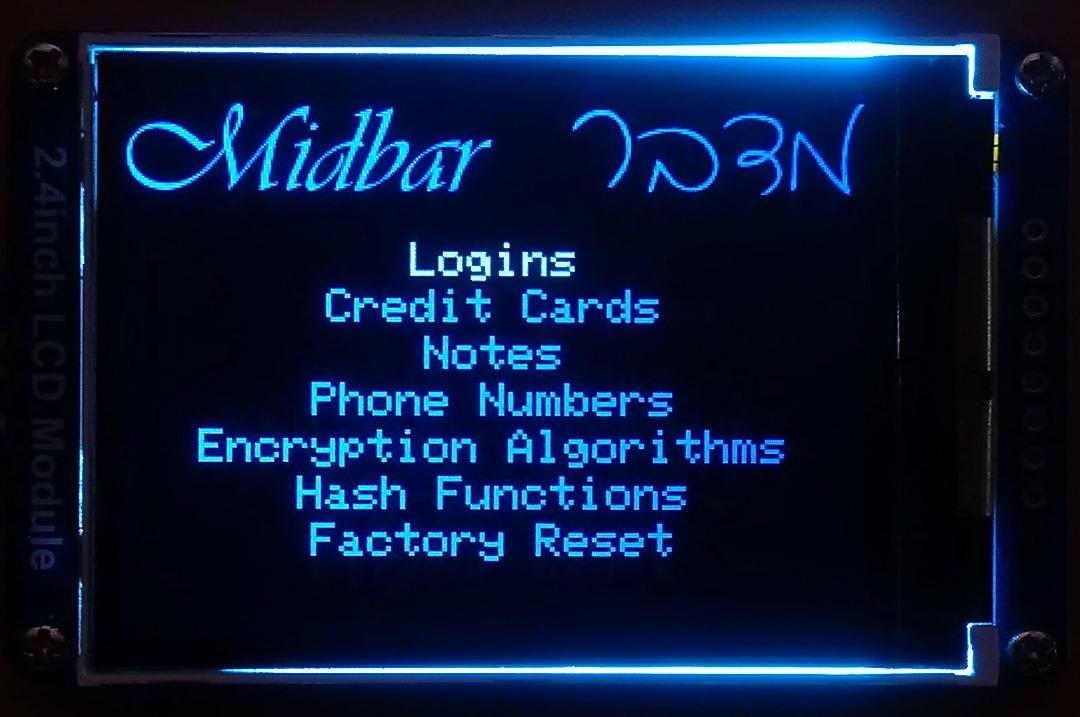
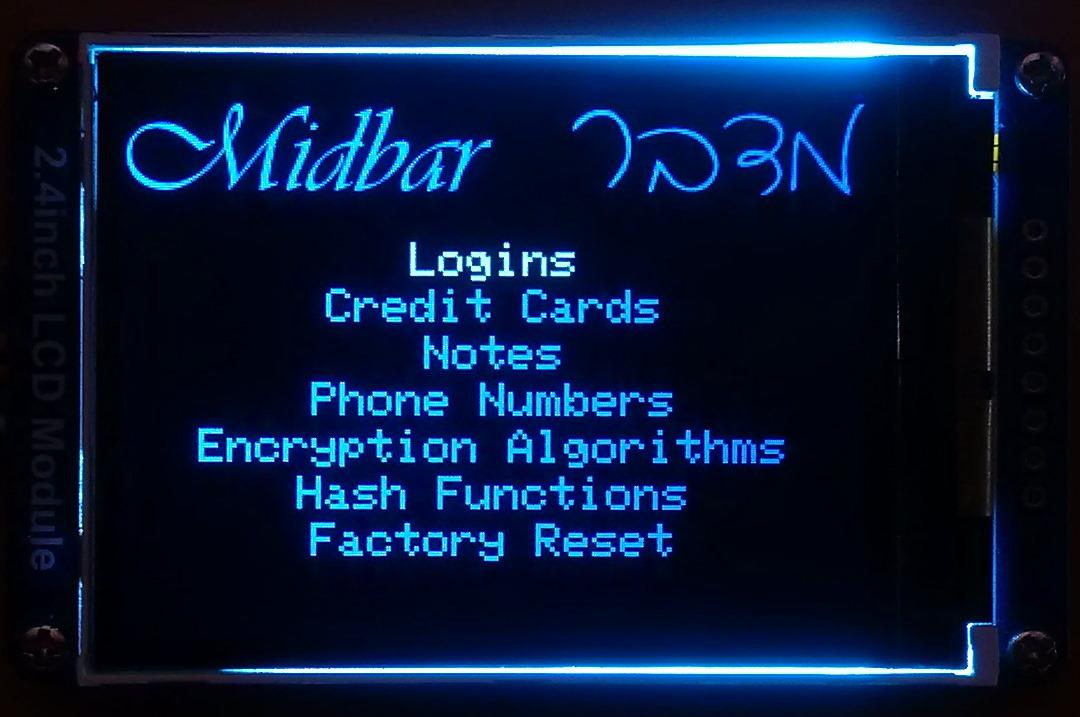
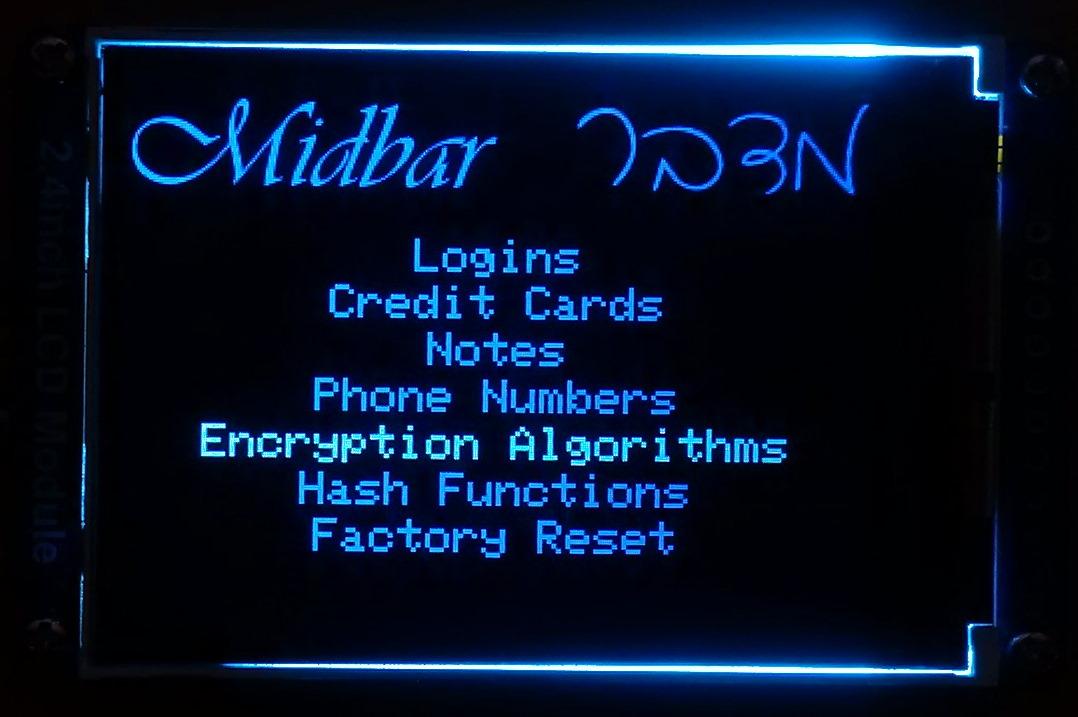
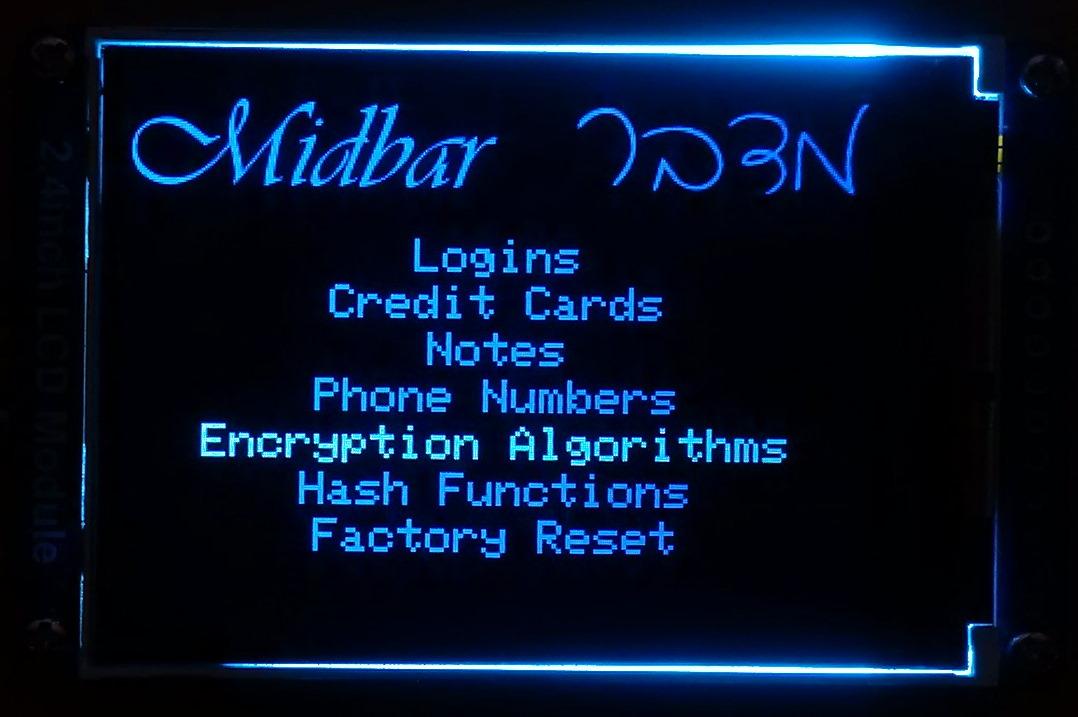
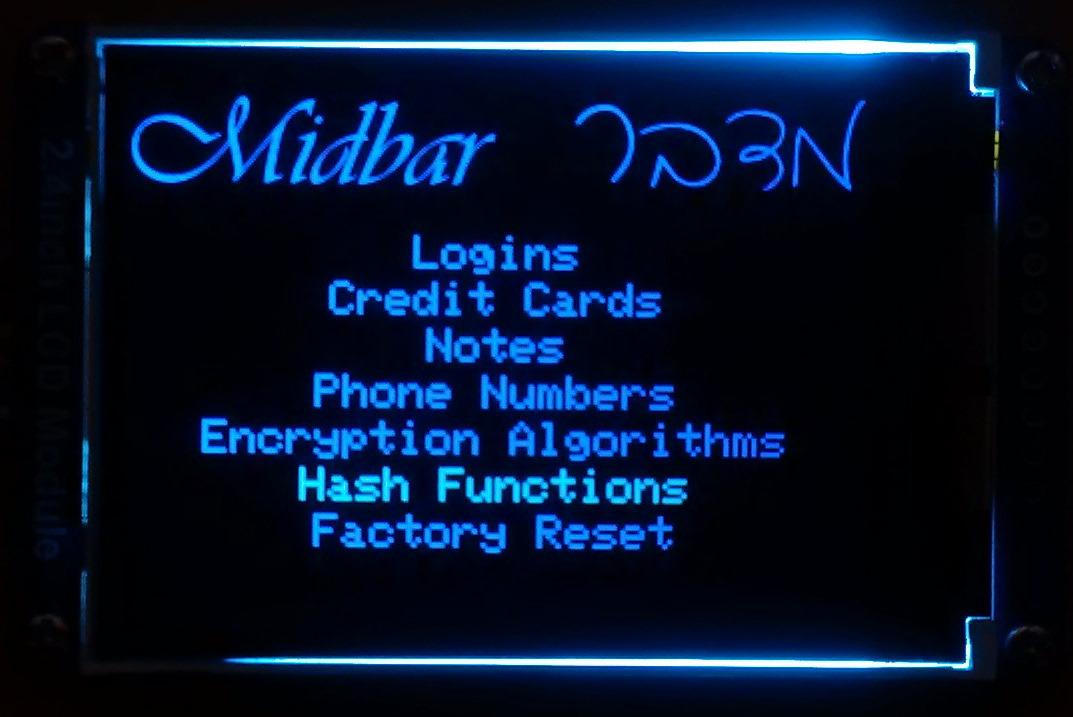
After you've unlocked the vault and got to the main menu:
- Either turn the rotary encoder to the right or press the "↓" (DOWNWARDS ARROW) key on the PS/2 keyboard to go down the menu.
- Either turn the rotary encoder to the left or press the "↑" (UPWARDS ARROW) key on the PS/2 keyboard to go up the menu.
- Press either the "A" button or the "Enter" key on the PS/2 keyboard to open the selected menu.
- While in the submenu, press either the "B" button or the "Esc" key on the PS/2 keyboard to return to the main menu.
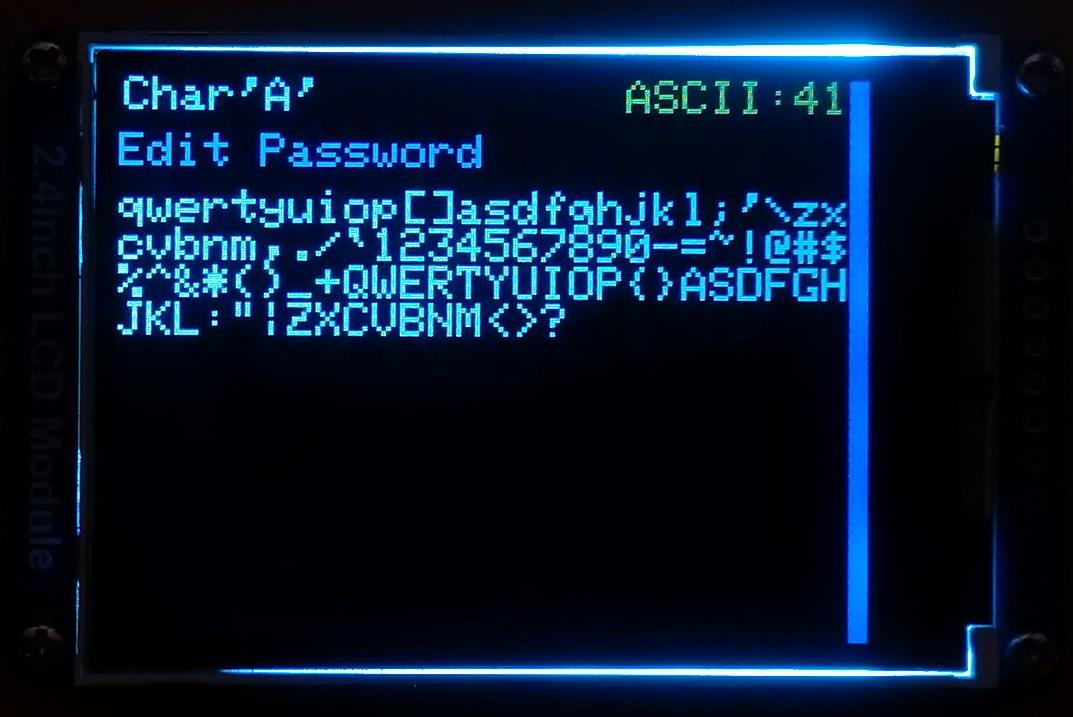
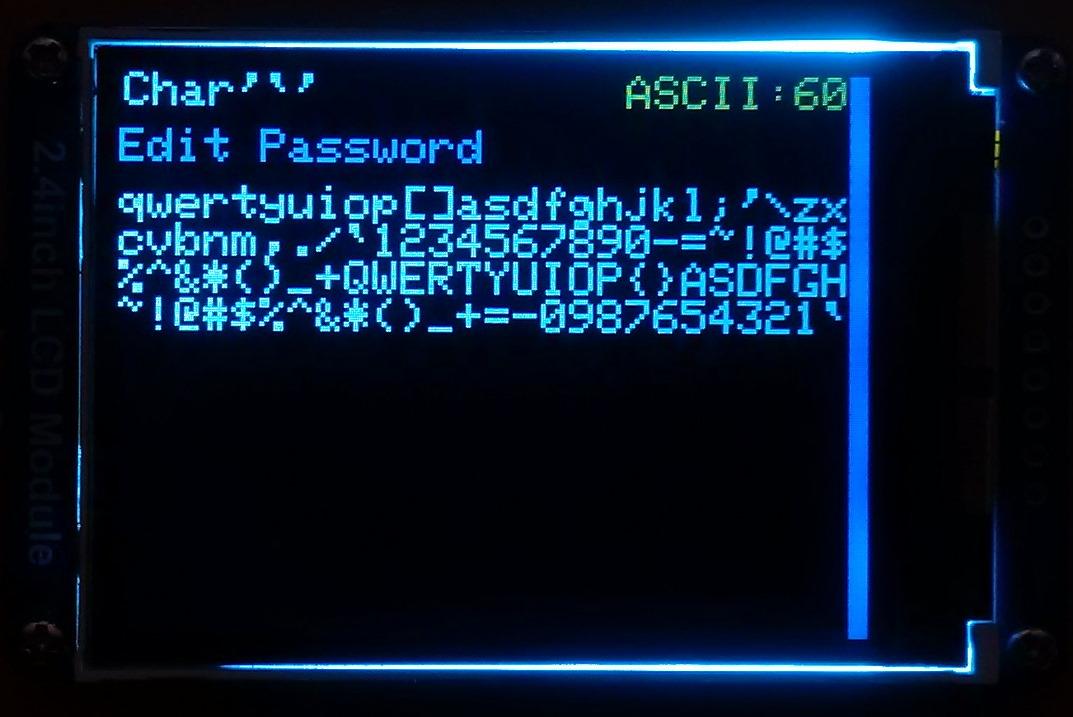
While entering a text in a tab:
- Either quad-click the encoder button four or press "Enter" on the PS/2 keyboard to continue;
- Either quintuple-click the encoder button (click it five times in quick succession) or press the "Esc" button on the PS/2 keyboard to cancel the current operation.
*If the hex value decreases when you rotate the encoder to the right, I would advise you to swap the wires connected to the GP12 and GP13 pins.
And by the way, pressing the "Caps Lock," "Num Lock," or "Scroll Lock" buttons makes the keyboard unresponsive until you either reconnect it or disconnect the RPI from the power source.
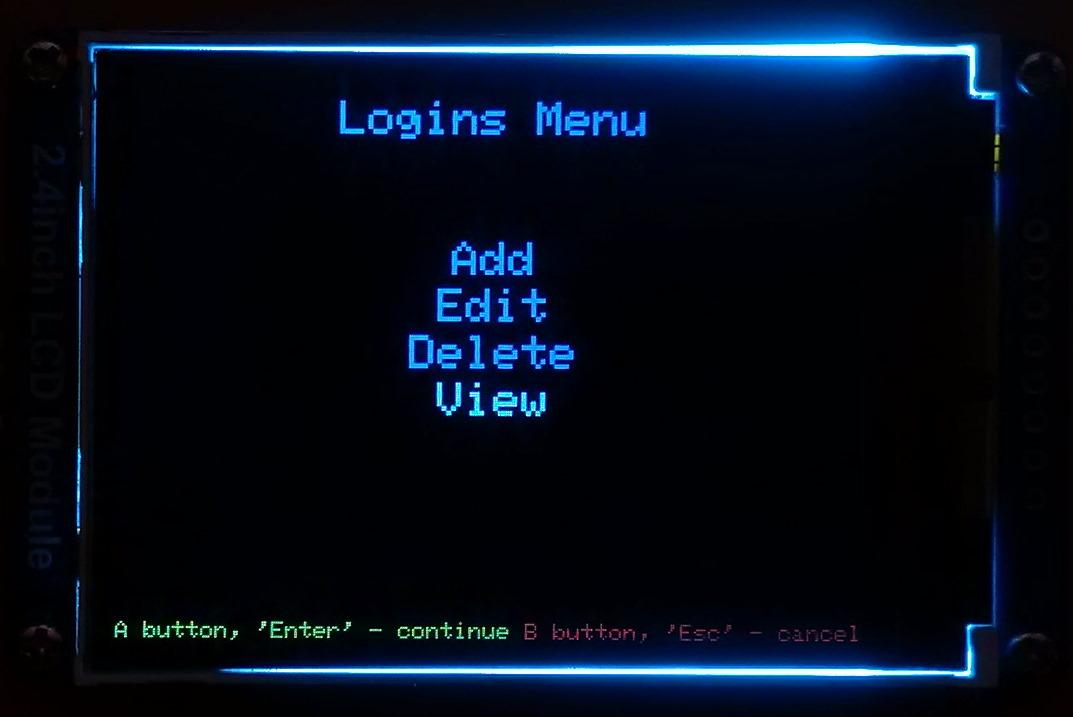
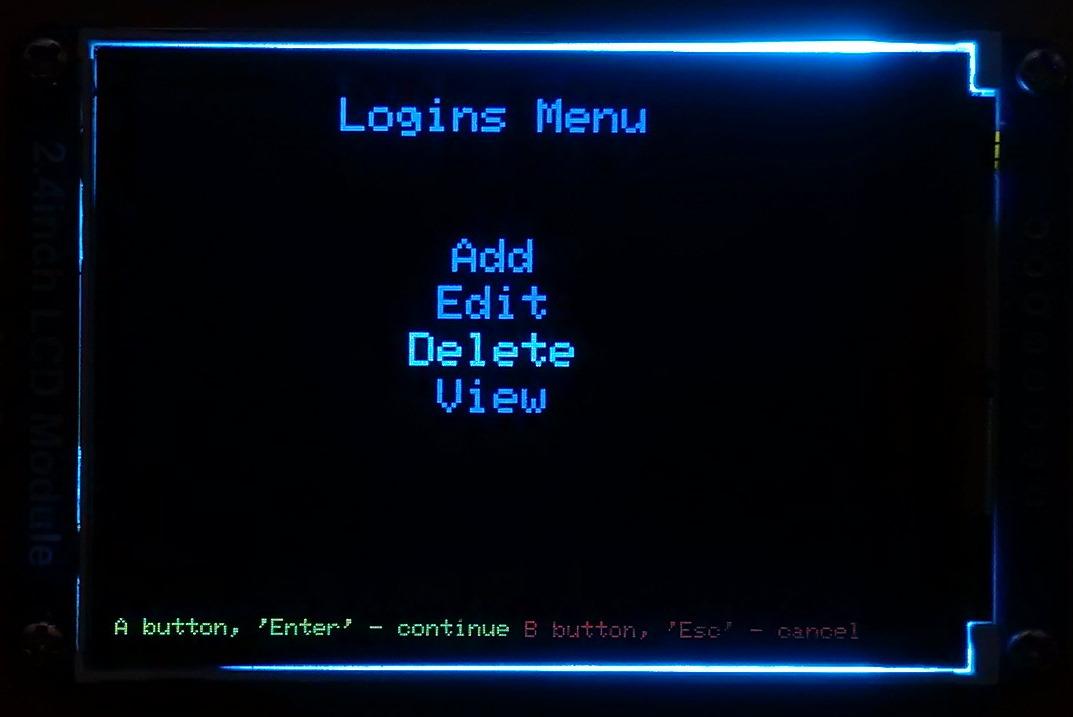
Add Login
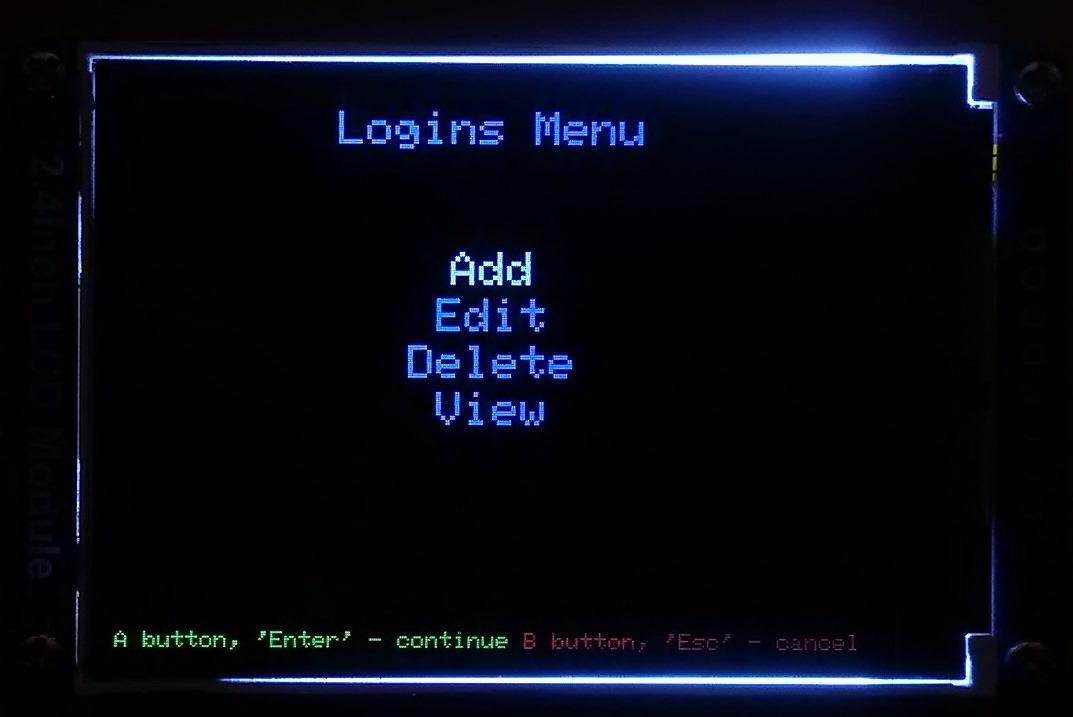
As I've mentioned in the introduction, the vault capability from the Midbar V2.5 is intact. The Raspberry Pi Pico version of Midbar utilizes the 3DES + AES + Blowfish + Serpent encryption algorithm with an integrity verification feature alongside the LittleFS to keep your data safe and organized.
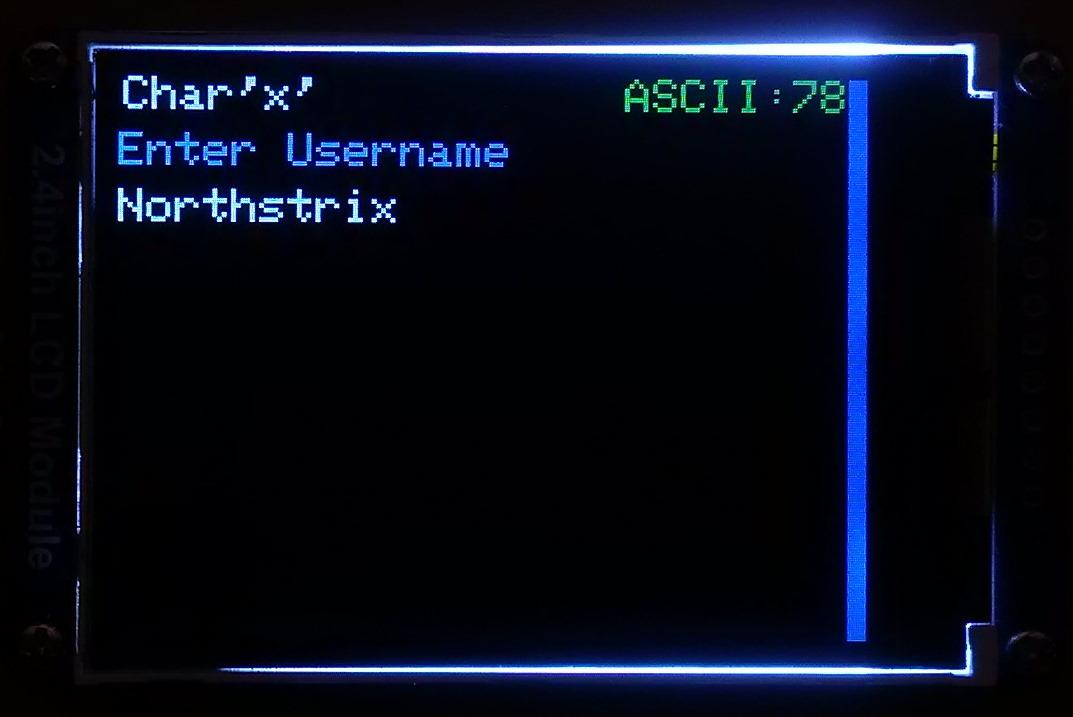
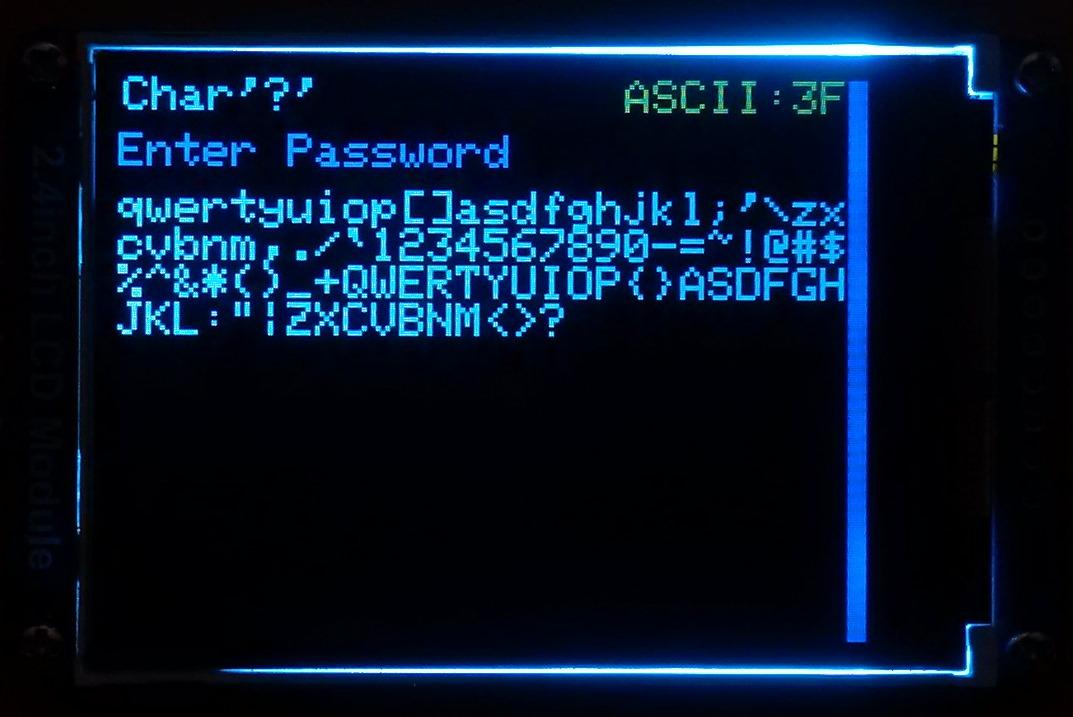
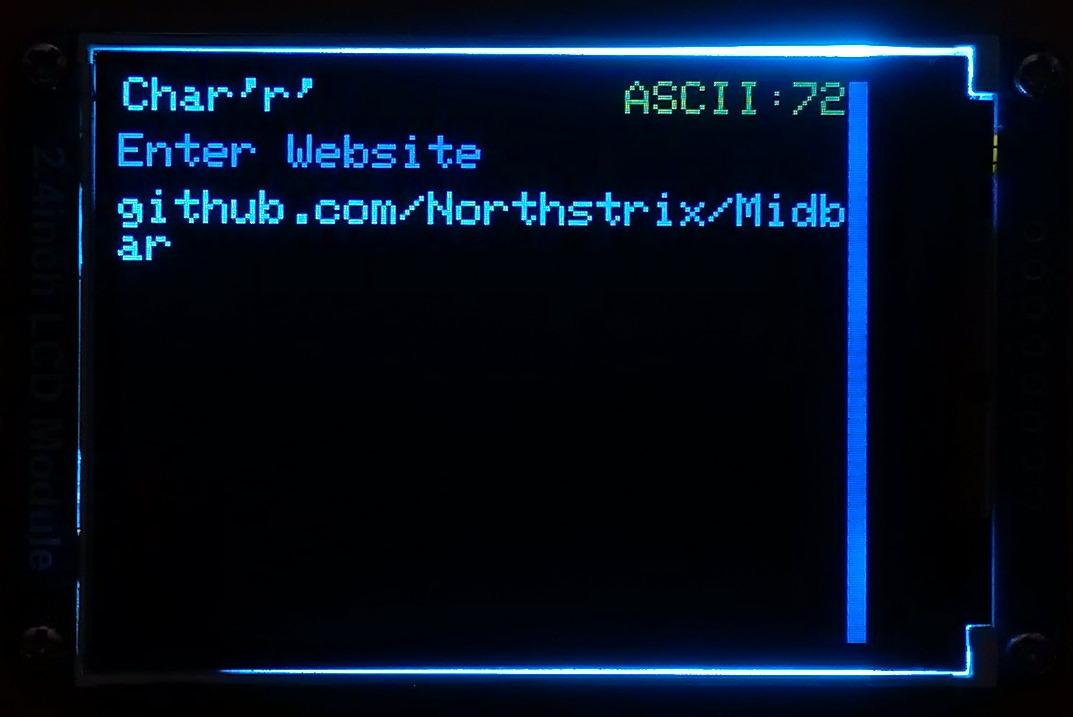
To add a login from the encoder and PS/2 keyboard:
- Select the "Logins" line in the main menu;
- Press either the "A" button or the "Enter" key on the PS/2 keyboard;
- Select the "Add" line;
- Press either the "A" button or the "Enter" key on the PS/2 keyboard;
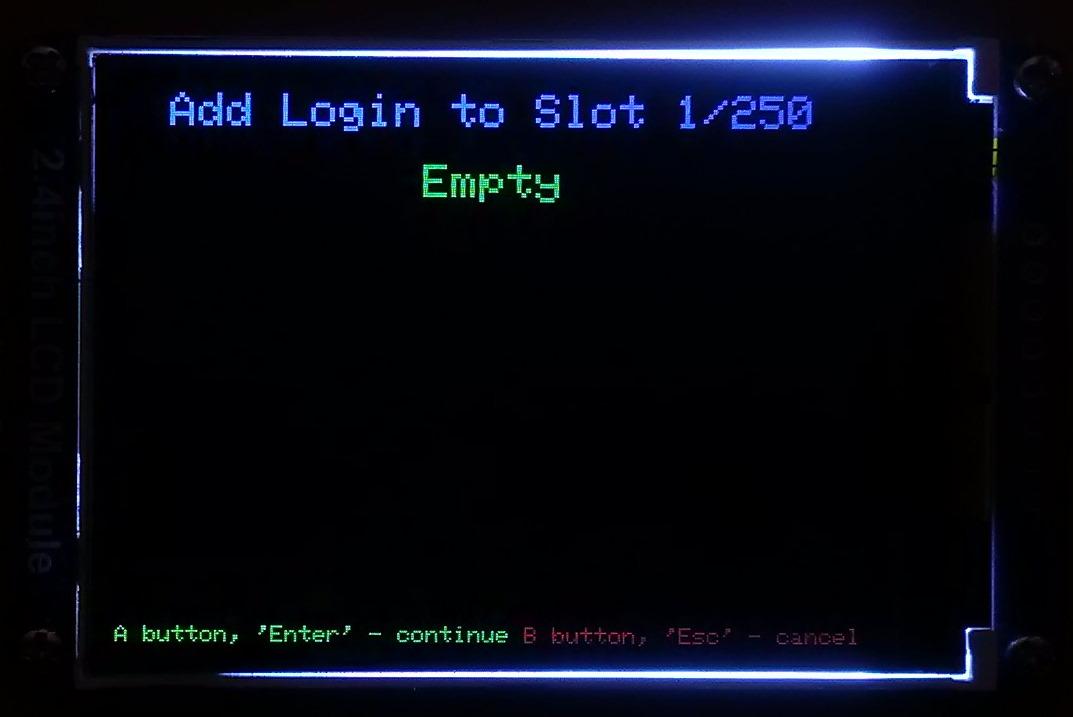
- Choose the slot you want to put the login to either by rotating the encoder or by pressing the "←" (Leftwards Arrow) and "→" (Rightwards Arrow) keys on the PS/2 keyboard;
- Press either the "A" button or the "Enter" key on the PS/2 keyboard;
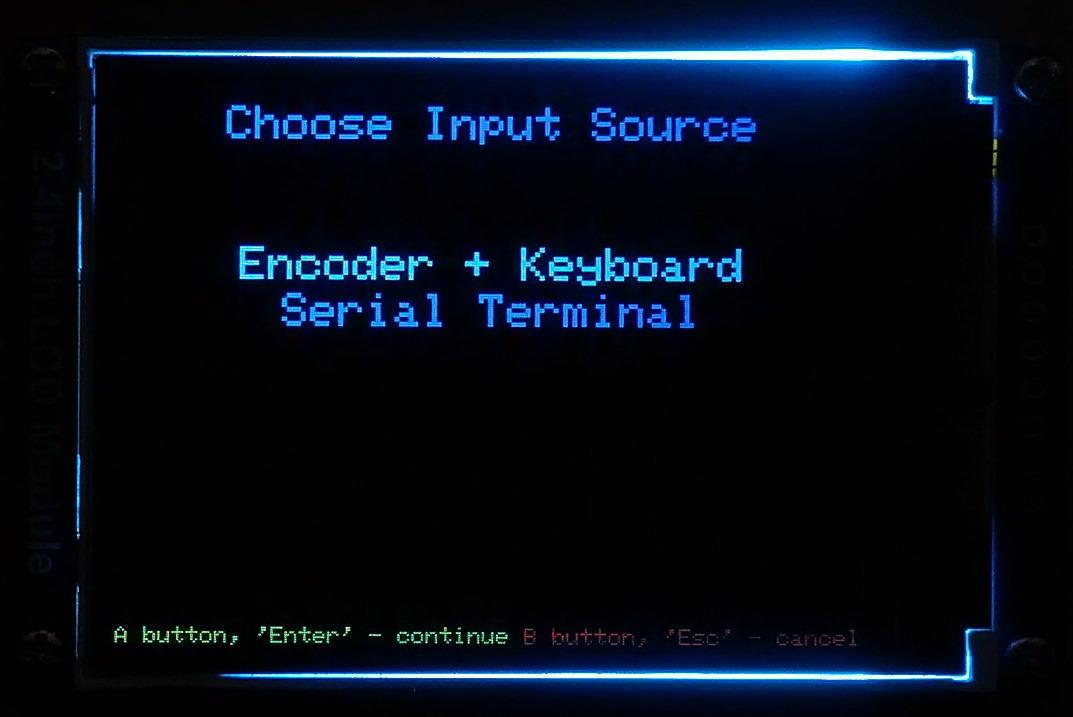
- Select the "Encoder + Keyboard" line;
- Press either the "A" button or the "Enter" key on the PS/2 keyboard;
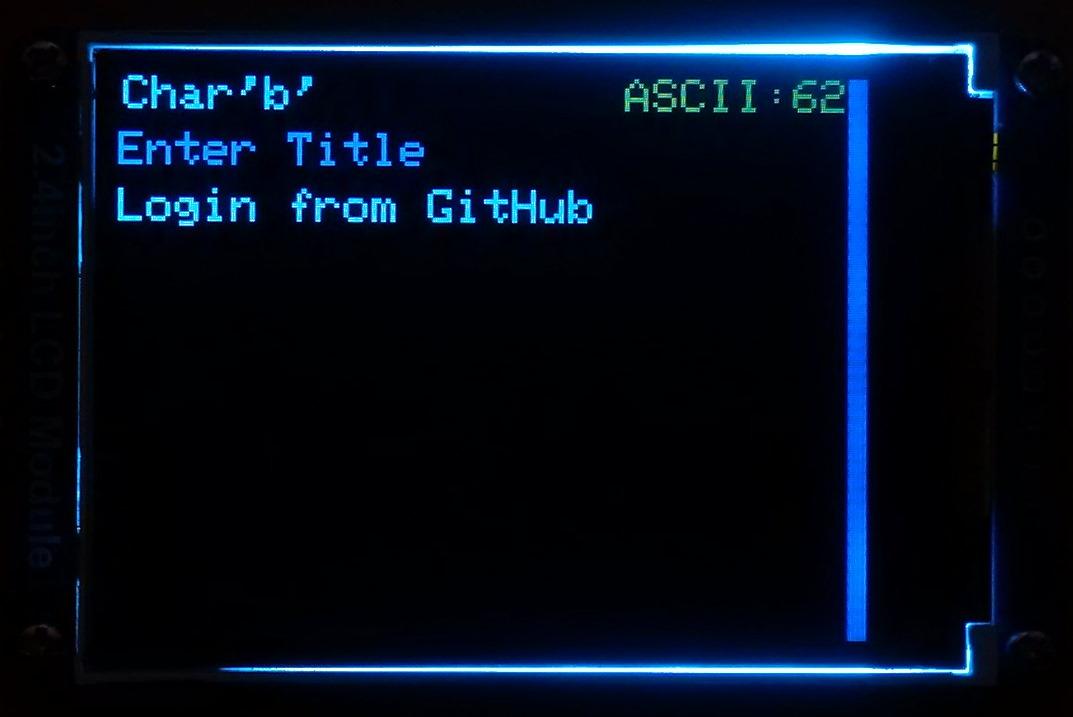
- Enter the title;
- Either quad-click the encoder button or press "Enter" on the PS/2 keyboard;
- Enter the username;
- Either quad-click the encoder button or press "Enter" on the PS/2 keyboard;
- Enter the password;
- Either quad-click the encoder button or press "Enter" on the PS/2 keyboard;
- Enter the website;
- Either quad-click the encoder button or press "Enter" on the PS/2 keyboard.
According to the tests I've conducted - Raspberry Pi Pico can encrypt and decrypt a 10000-character long string without any problems using the 3DES + AES + Blowfish + Serpent encryption algorithm. So, technically, you can put 10 000 characters into a field of a record.
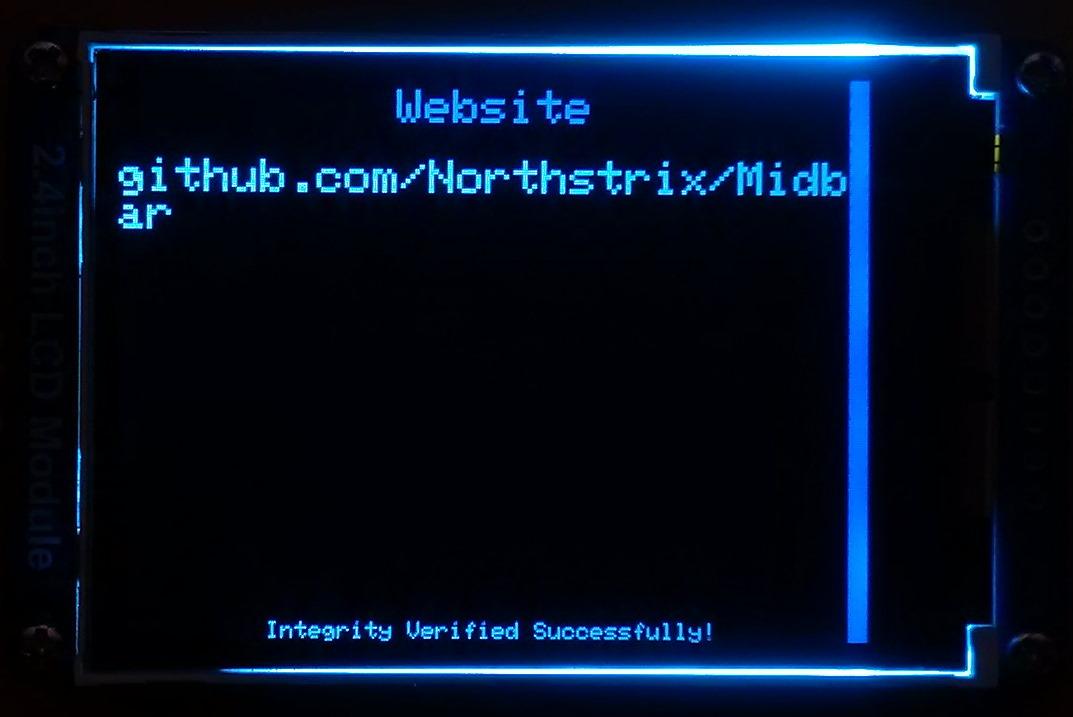
*All credentials demonstrated here are entirely fictitious. Any similarity to actual credentials is purely coincidental.
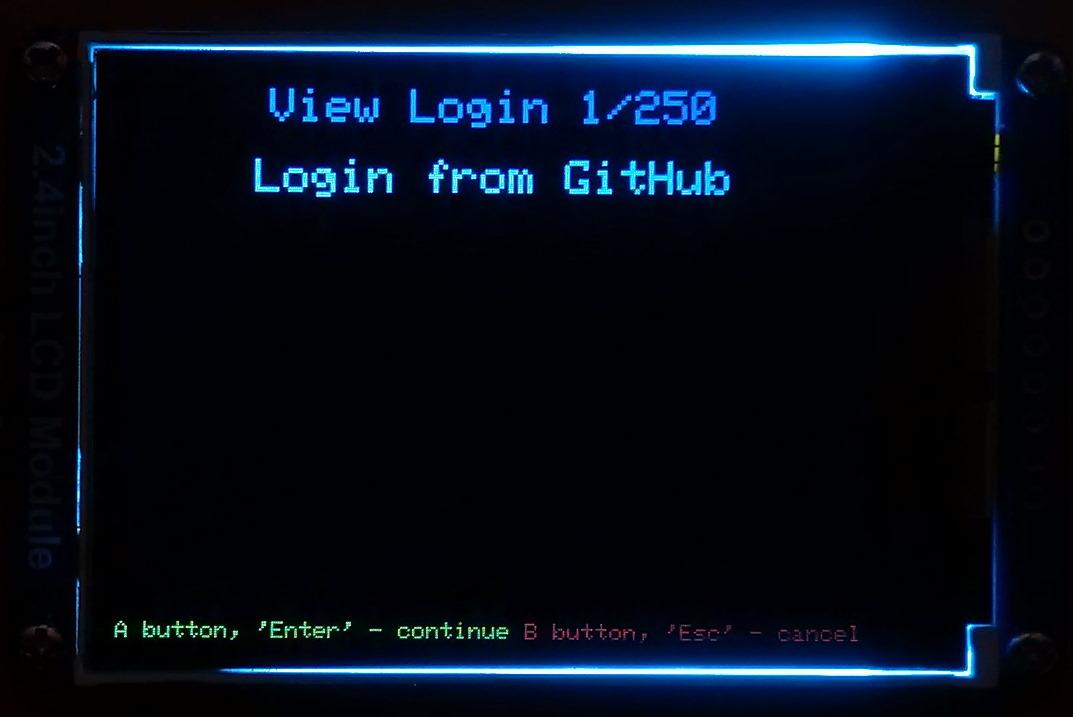
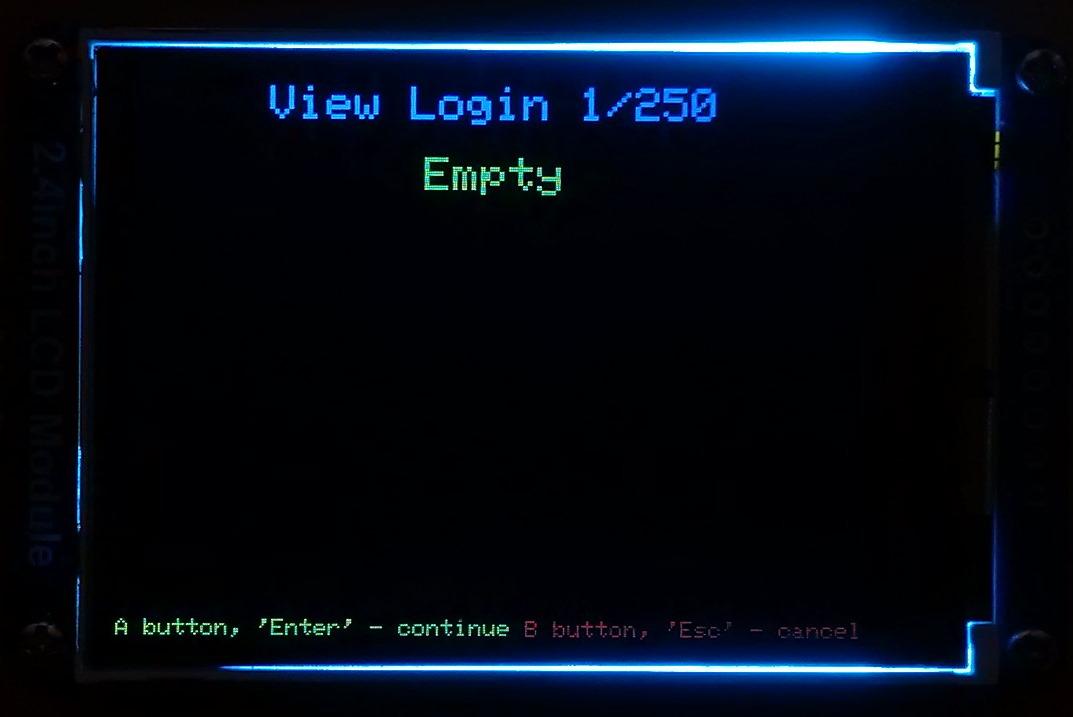
View Login
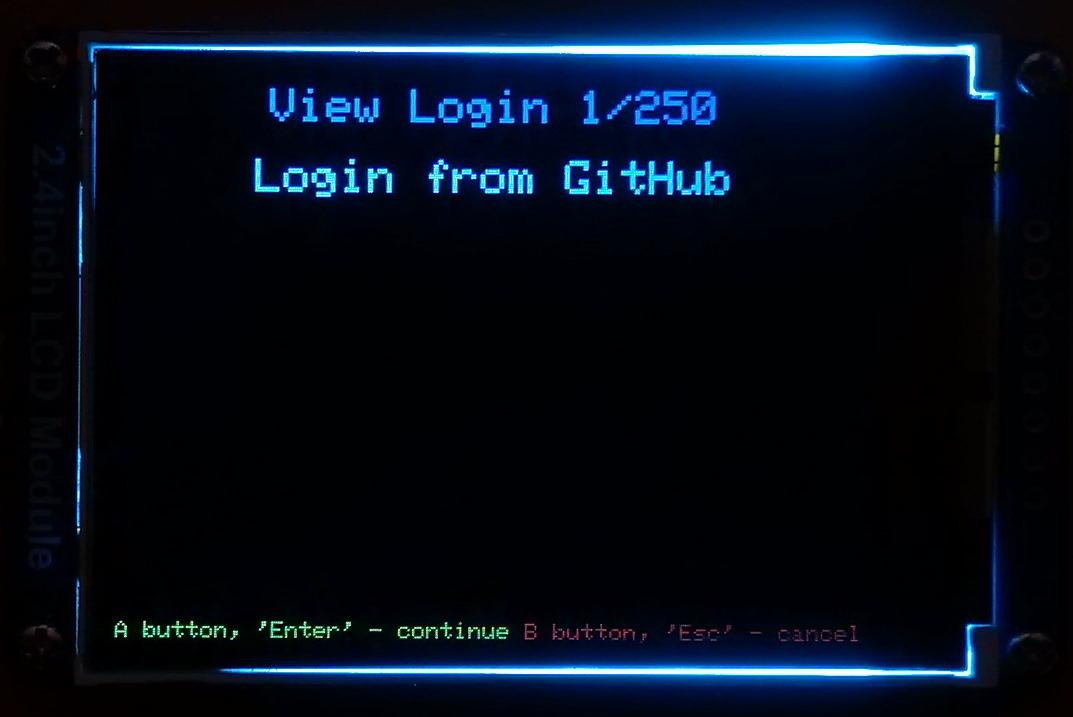
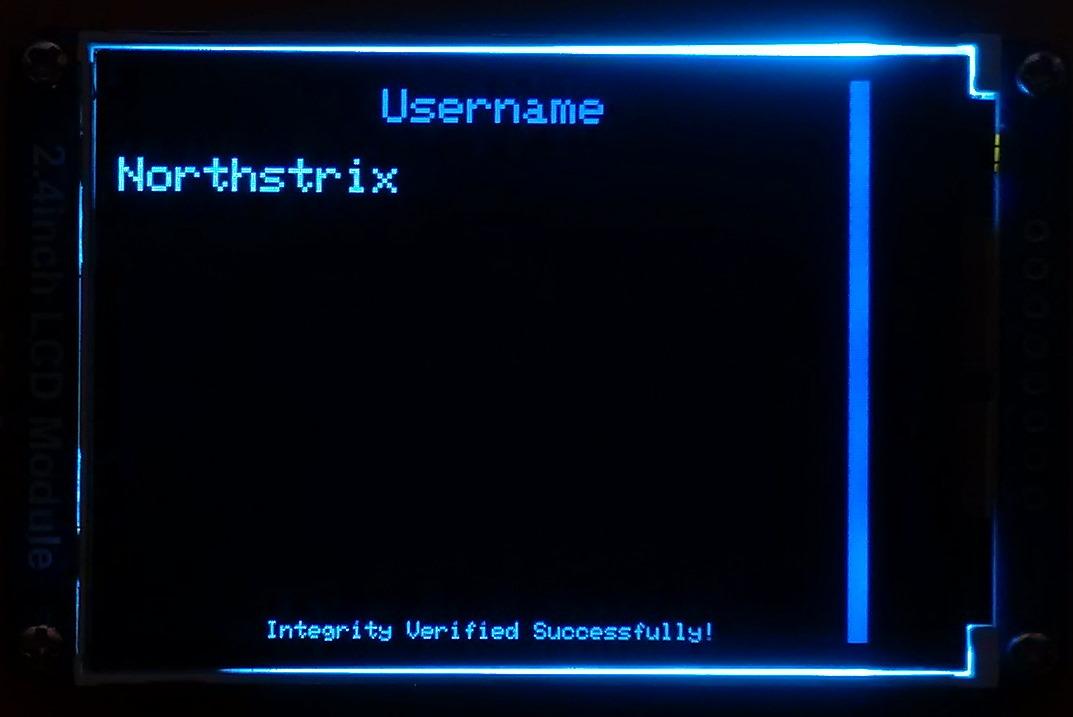
To view a login:
- Select the "Logins" line in the main menu;
- Press either the "A" button or the "Enter" key on the PS/2 keyboard;
- Select the "View" line;
- Press either the "A" button or the "Enter" key on the PS/2 keyboard;
- Choose the slot you want to view login from either by rotating the encoder or by pressing the "←" (Leftwards Arrow) and "→" (Rightwards Arrow) keys on the PS/2 keyboard;
- Press either the "A" button or the "Enter" key on the PS/2 keyboard;
- Press any key to view the content of the next field.
*All credentials demonstrated here are entirely fictitious. Any similarity to actual credentials is purely coincidental.
Edit Login
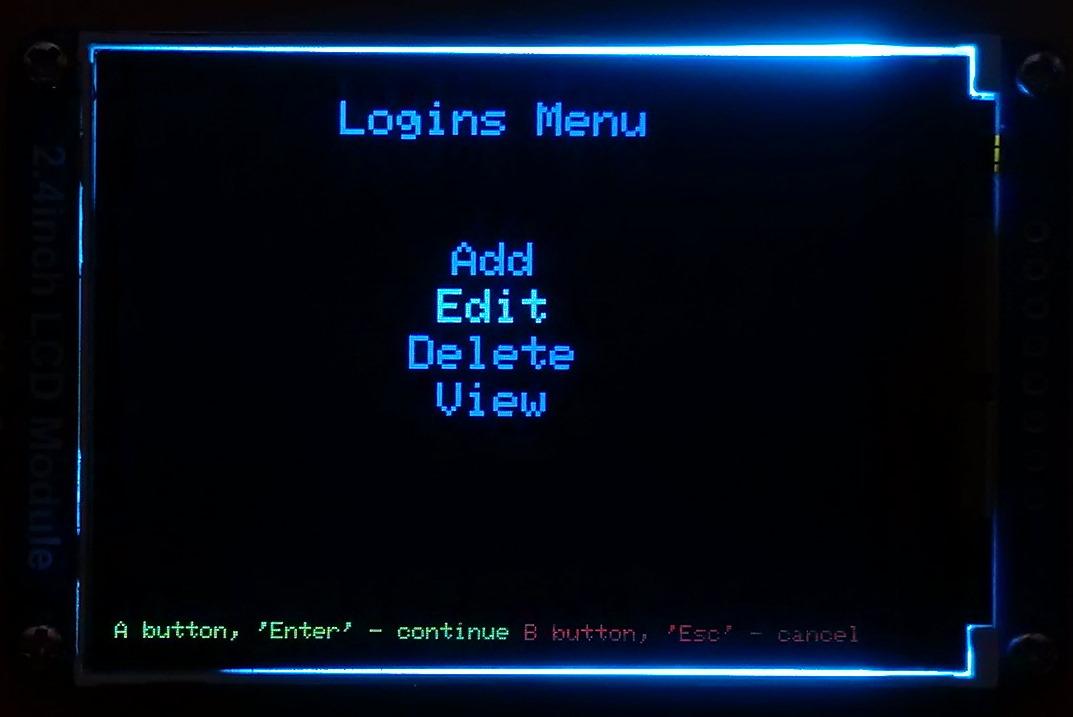
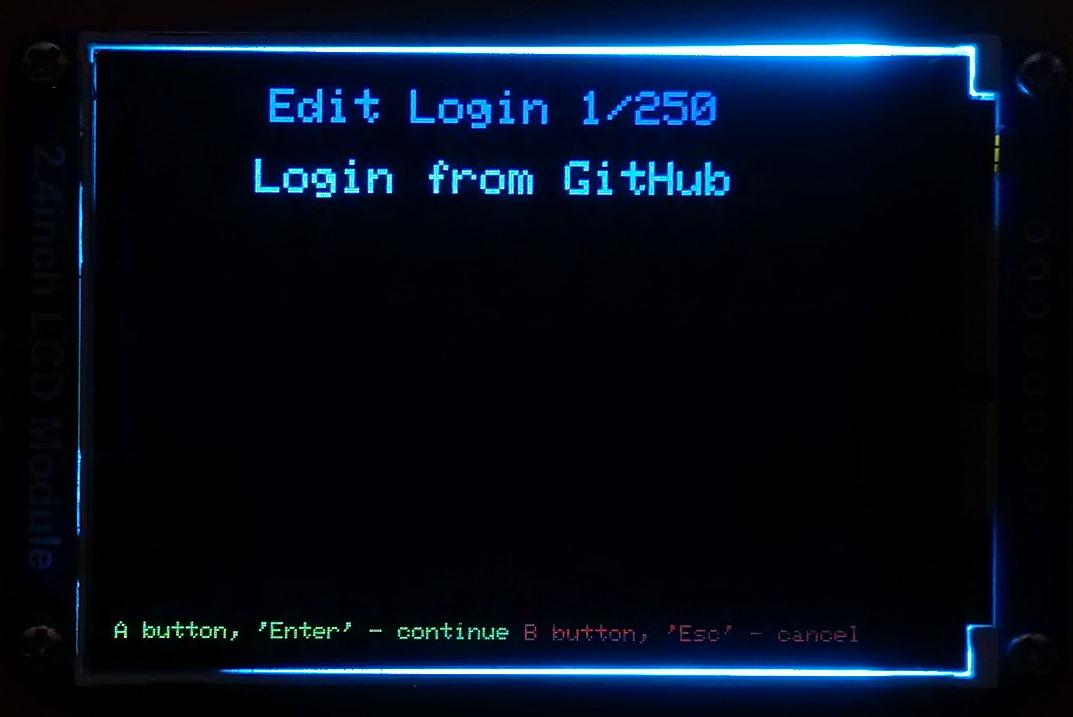
To edit a login:
- Select the "Logins" line in the main menu;
- Press either the "A" button or the "Enter" key on the PS/2 keyboard;
- Select the "Edit" line;
- Press either the "A" button or the "Enter" key on the PS/2 keyboard;
- Select the login you would like to edit either by rotating the encoder or by pressing the "←" (Leftwards Arrow) and "→" (Rightwards Arrow) keys on the PS/2 keyboard;
- Press either the "A" button or the "Enter" key on the PS/2 keyboard;
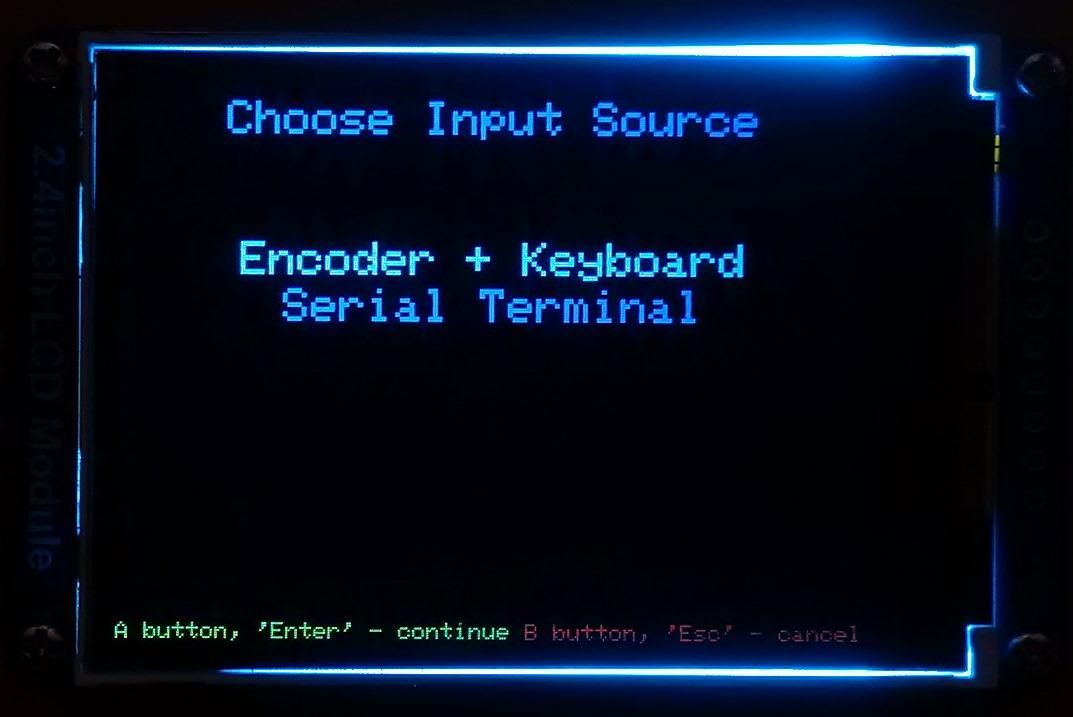
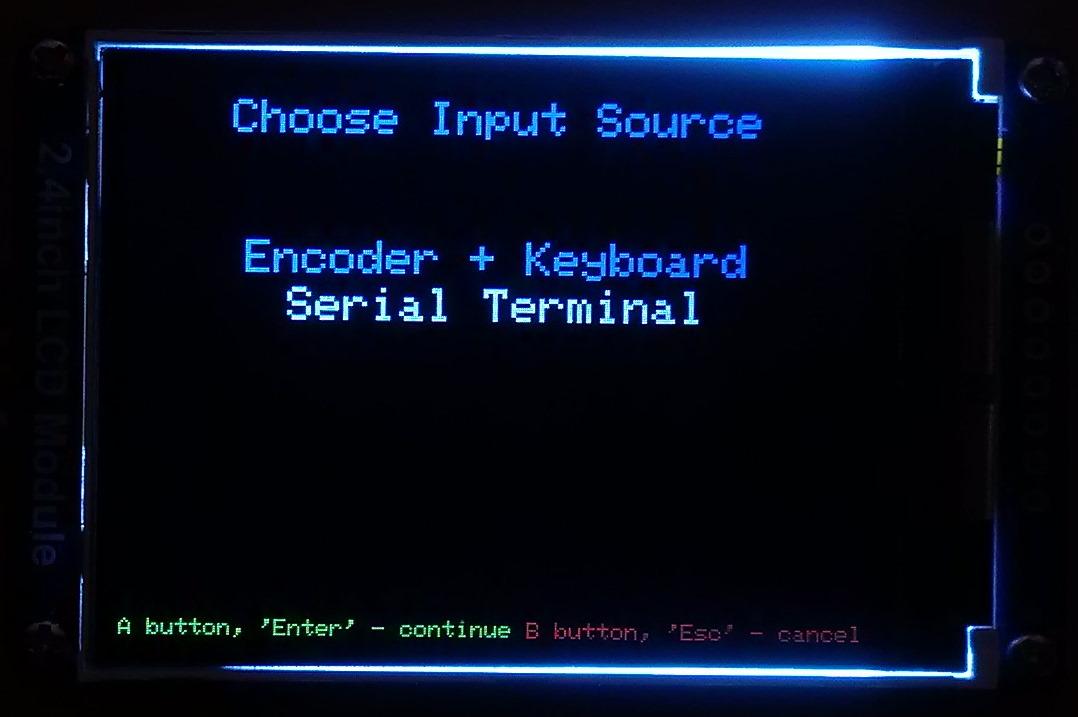
- Select the input source;
- Press either the "A" button or the "Enter" key on the PS/2 keyboard;
- Depending on the chosen input source, either enter the new password you'd like to set on the encoder and PS/2 keyboard or paste it to the Serial Terminal;
- Depending on the chosen input source, either quad-click the encoder button (or press "Enter") or press the "Send" button in the Serial Terminal.
*All credentials demonstrated here are entirely fictitious. Any similarity to actual credentials is purely coincidental.
Delete Login
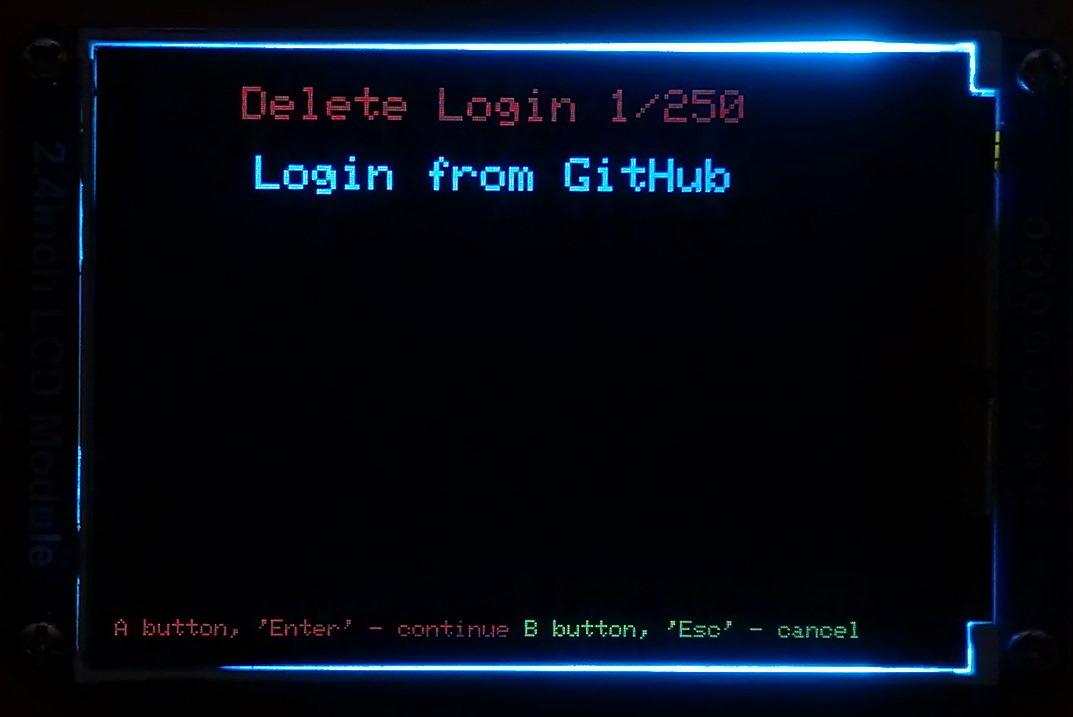
To delete a login:
- Select the "Logins" line;
- Press either the "A" button or the "Enter" key on the PS/2 keyboard;
- Select the "Delete" line;
- Press either the "A" button or the "Enter" key on the PS/2 keyboard;
- Select the login you would like to delete either by rotating the encoder or by pressing the "←" (Leftwards Arrow) and "→" (Rightwards Arrow) keys on the PS/2 keyboard;
- Press either the "A" button or the "Enter" key on the PS/2 keyboard.
The process of working with records of other types is very similar to the process of working with logins.
Encrypt String
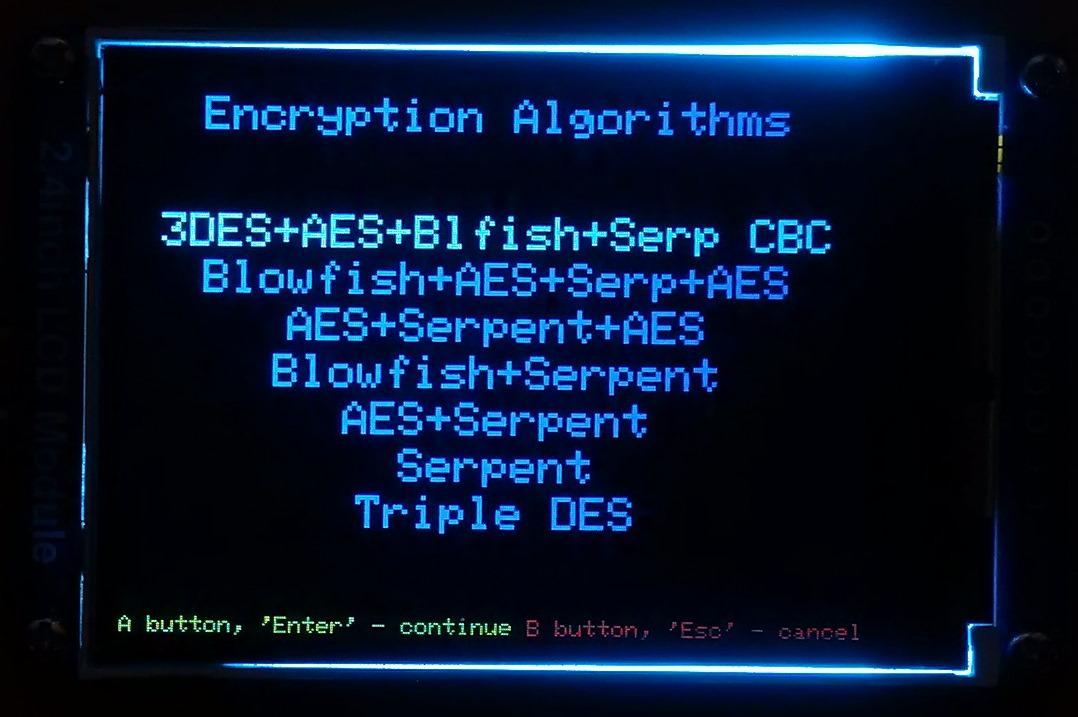
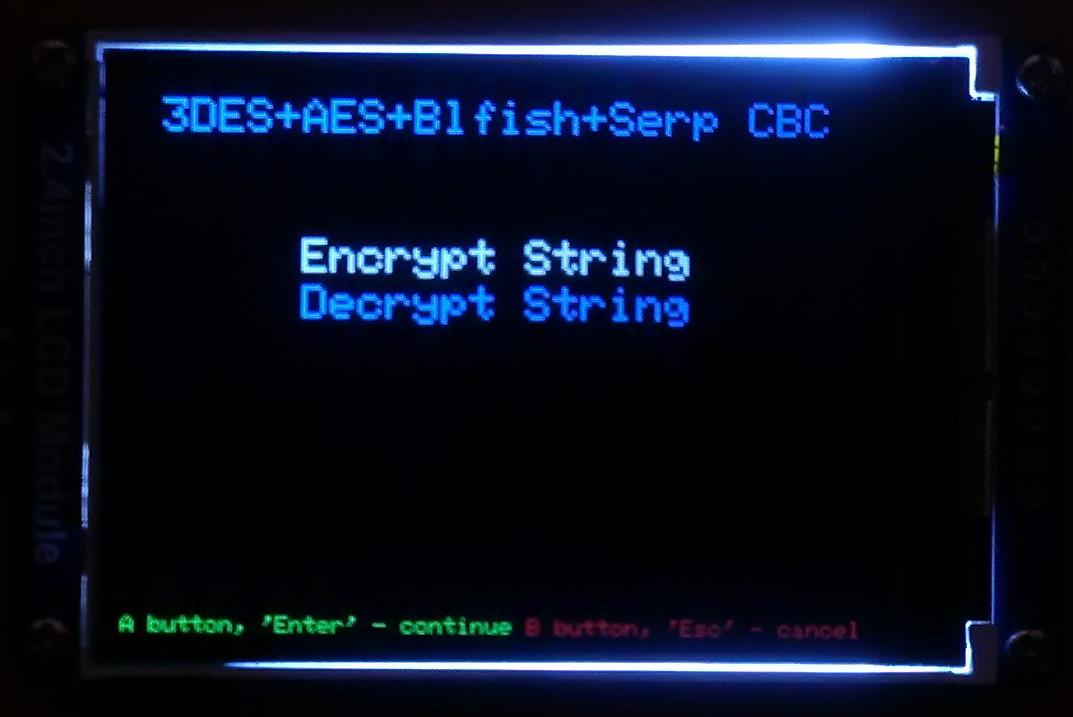
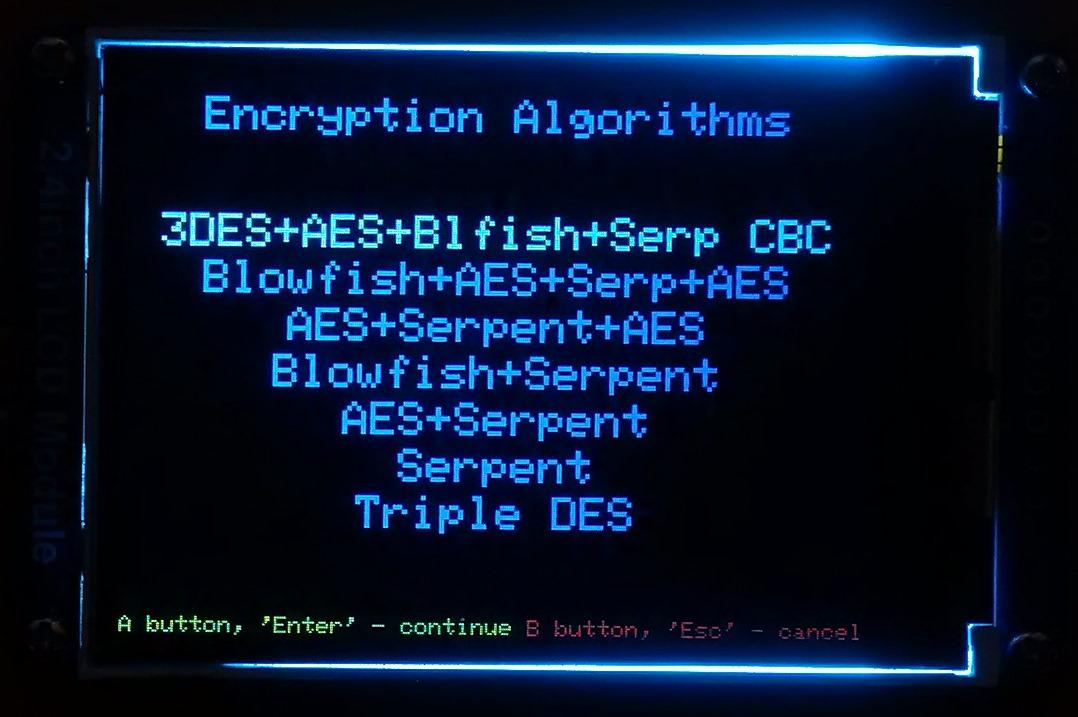
As I've mentioned before, Midbar utilizes seven encryption algorithms. You can use any of them to encrypt your data.
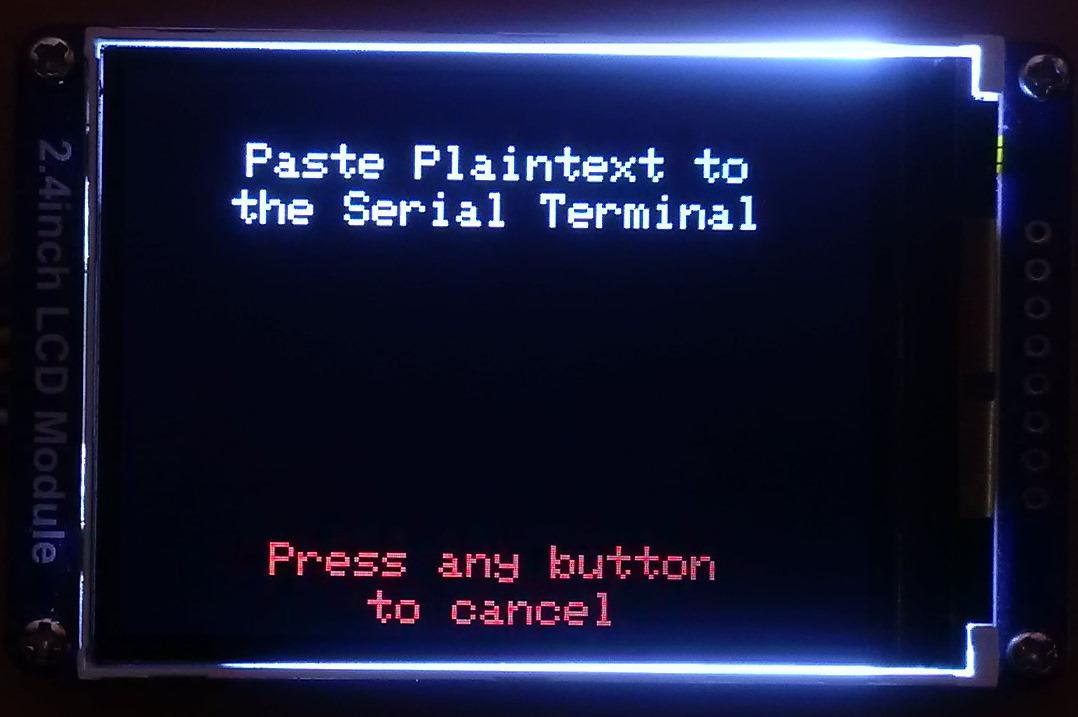
To encrypt text:
- Open the Serial Terminal because the ciphertext will be printed to it;
- Select the "Encryption Algorithms" line in the main menu;
- Press either the "A" button or the "Enter" key on the PS/2 keyboard;
- Select the line with the name of the encryption algorithm you would like to use;
- Press either the "A" button or the "Enter" key on the PS/2 keyboard;
- Select the "Encrypt String" line;
- Choose the input source;
- Press either the "A" button or the "Enter" key on the PS/2 keyboard;
- Depending on the chosen input source, either enter the text you'd like to encrypt on the encoder and PS/2 keyboard or paste it to the Serial Terminal;
- Depending on the chosen input source, either quad-click the encoder button (or press "Enter") or press the "Send" button in the Serial Terminal.
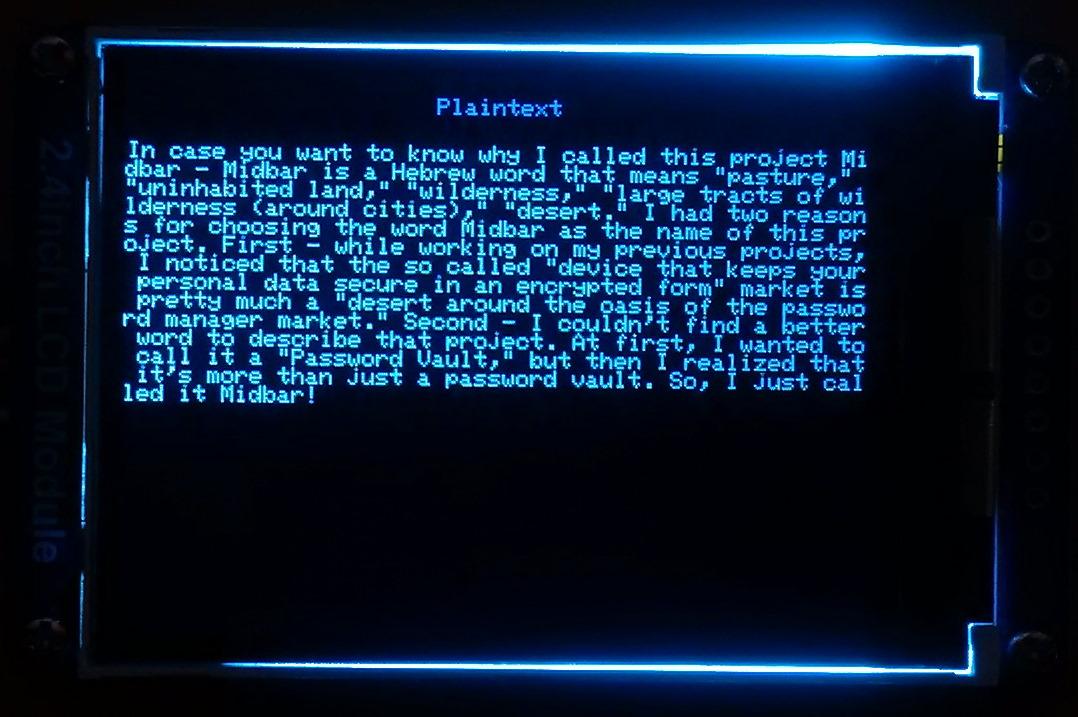
Plaintext:
In case you want to know why I called this project Midbar - Midbar is a Hebrew word that means "pasture," "uninhabited land," "wilderness," "large tracts of wilderness (around cities)," "desert." I had two reasons for choosing the word Midbar as the name of this project. First - while working on my previous projects, I noticed that the so called "device that keeps your personal data secure in an encrypted form" market is pretty much a "desert around the oasis of the password manager market." Second - I couldn't find a better word to describe that project. At first, I wanted to call it a "Password Vault," but then I realized that it's more than just a password vault. So, I just called it Midbar!
Ciphertext:
d4c57216bdf65992892e91e2651db53d51509c07c7ce90334aa79faa0aa8dc3867ca84498332913f391546c2162fccff7664e29db8a23a49e22dc8b4fe79023bc755f3dc271f532be781b97951ac01539127bbfac028c364426e8500d683f1e4dc05da52f31fc5698016ebdb2d54feb51fc65b2692bb271a79e5714e03715b03950e1b87088d5de280f937ed1c7bbec77dea4e0de869e51a4bc20a2ba114b751614a33c061d4d9d4e46b251caa88a872c8d1a1ab61f432b4f813276d1e31e027e60c90a3abd79cd9266689f24956f822a197948491da7ee5da13c0976bf89b5bd433250679c2e91f4d56c6d11c6f8cd70d878bc6af6cf12fb2a191b3c2f5037e233f3648da89570b76418b9fb6afbc6053bd62c0d741fdb946a279c0cd271cd291ca753343646e610bfbdc8860974b52bb00128e852dc153ea67b50aace4261eef54f9a98eb4c091d725c7d4aed8f136e426723a3c2c9ad70431d310b0dc118e86fe8ee566c627d2d1ab463c5782d77aebc37221760535b4d106ef6dc41e89b7557ea75f6525e192d87fb828b5f2d5a71fa8812a1cb7b1054c63343ba2552a93c90e34a0fbf9043593359225cf25df1f67af76989d1ad70d55ef27ab05d56376dfb903332466be419ecd6eece62d16dc2ae7f2dc8c544af9649bb22b1a857880e7134ba824c5d0d0941a81b218edf82294744cac26720ad0ed49d29b1afaed545b5c7da0c33a9a9ace783eb0808c02c8b64723c26fb93cbfe036611f84433004de3c45f13e211fa59e89e8651a170719d1c73d0a2ecaba2b5d3c9b006d77d01f9f37a45ff61a296ed2db282edbe0a10f8a26bfd9d170e4b34ddff8cf08b62356c668580b757899e9dcfbe4dbfaee0c70a9715d6af105591ae59240ed9fae09eaba4b8813866fecf0e1061ee44a43a4ed49658ab8414c8f32e144a52a7b1e7cbfa15fbf9043f87b42c9be8cd1d4d93a00a11a8620945f9dbfe1f75d2ab8ba8009a8e373590640a1cc09fb03b613ddf619880b9b026e333bb0eea39f3bc644c8e0c6ffa8f083efbf369ea496fdbffbe76bbb7aaf9f563d276efa718c416993d7e1ac0b073ff7400d73ed80c2408cc9b3c9b15795c2dcd49581fd39180a606f5c4bcc8ec48b01ef536bf1dd72fe80a69399ac88fbbd01d3af7a9b176a9764bd09a79d41eb3a515ebaa9610393079fbf5ed06d724f37e6cd936d2bd9600c6f0a8588aca88c02061dbb9ab72eeb1809627eb21d8df5c6cf420fa9b6ec0e97d433589669f7a3883a8a980cb0b1f5110f18ddb54f22336c28bafe6f5e7ee2267cbc17c776299a3d04652a984de59eb58b028a25da2549fefa795a51e36f9dece90b5a9e424c42d961b15600ce6d705bdfdada88b056ce0136773d7873ccaba956066320b1610fe67e4833a88baaf3e76c7004db1571112c12b3bf8357f1dc9681a106f7bf8247d8304601b210c820bedcac1d2a8f83fcfe712e03dab18a5107627d1092a054b19e85d57a6707e8fb5be8dd78273afb6897bcdaa17d2a314a2ca1c0436b6e2bb71fc09f4b42561e2bfc92ea188264b117d23712b7b6f23b486c6a477898bb9ca0c4f965cfc17bba797f61f4338689feff81c14562d166439b1a1a0cdf7dfb6543513ac8a86e38a277e6a221a6e1922933b12b7ac7373ce1ad64a0737b68632952c4cbcce5f1cbf458c48ac45ad8fac8ee61f28530f14dc68cb6351bf42e
Decrypt String
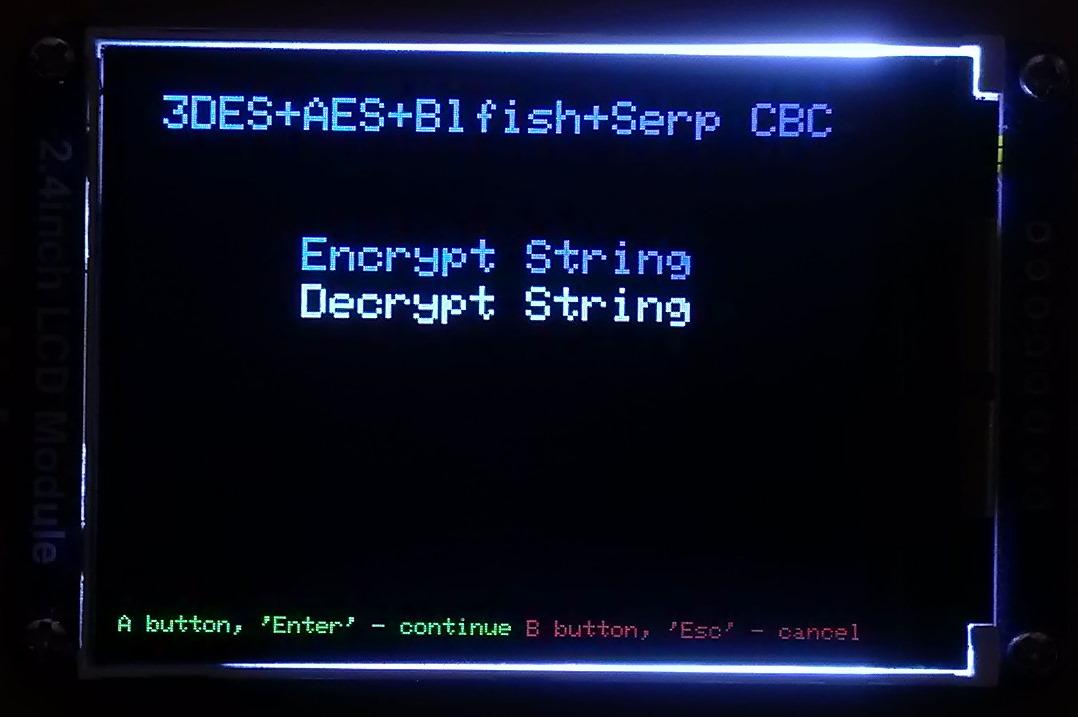
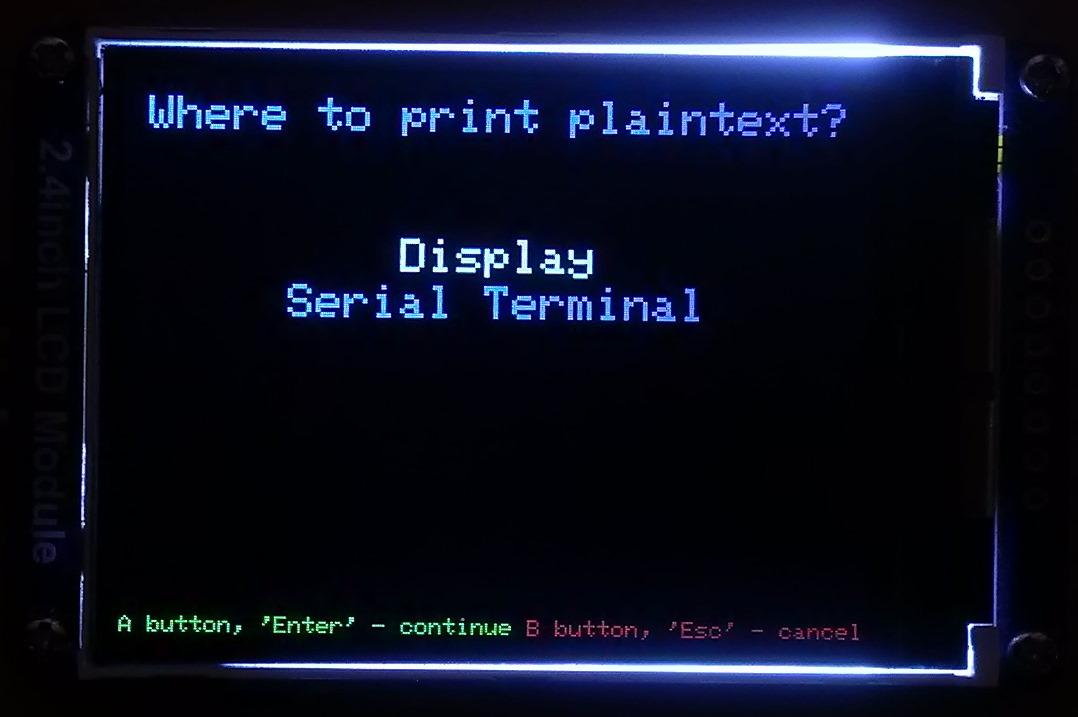
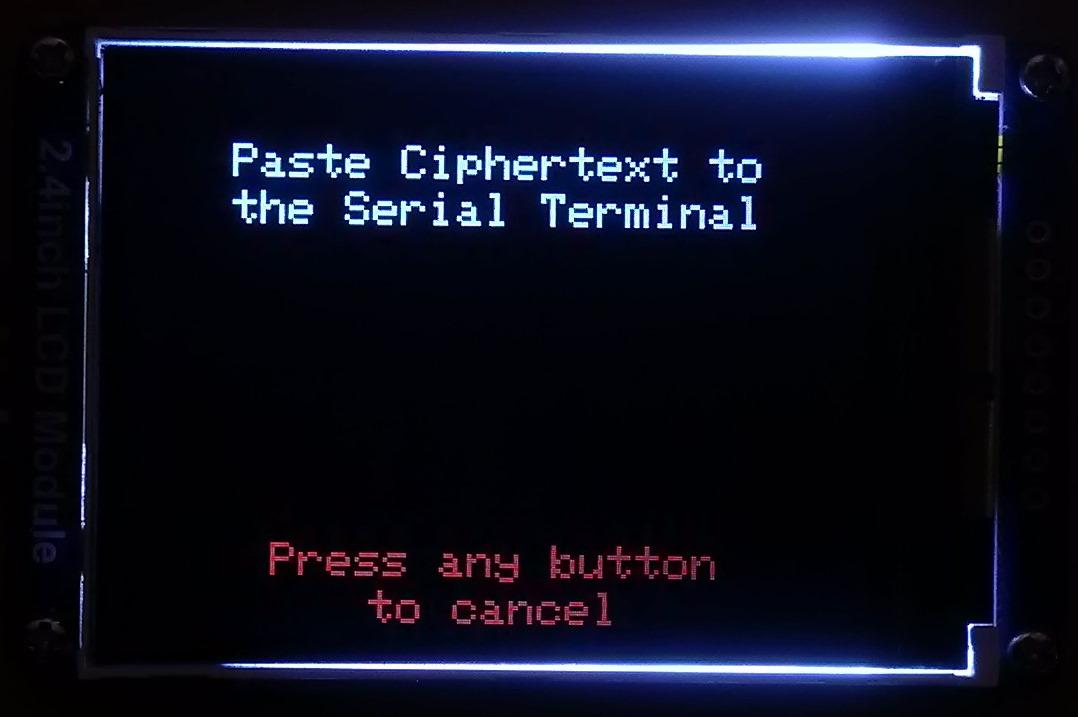
To decrypt text:
- Open the Serial Terminal because you'll need to paste the ciphertext to it;
- Select the "Encryption Algorithms" line in the main menu;
- Press either the "A" button or the "Enter" key on the PS/2 keyboard;
- Select the line with the name of the encryption algorithm you've used to encrypt the text;
- Press either the "A" button or the "Enter" key on the PS/2 keyboard;
- Select the "Decrypt String" line;
- Press either the "A" button or the "Enter" key on the PS/2 keyboard;
- Choose where to print the plaintext;
- Press either the "A" button or the "Enter" key on the PS/2 keyboard;
- Paste the ciphertext to the Serial Terminal;
- Press the "Send" button in the Serial Terminal.
Ciphertext:
d4c57216bdf65992892e91e2651db53d51509c07c7ce90334aa79faa0aa8dc3867ca84498332913f391546c2162fccff7664e29db8a23a49e22dc8b4fe79023bc755f3dc271f532be781b97951ac01539127bbfac028c364426e8500d683f1e4dc05da52f31fc5698016ebdb2d54feb51fc65b2692bb271a79e5714e03715b03950e1b87088d5de280f937ed1c7bbec77dea4e0de869e51a4bc20a2ba114b751614a33c061d4d9d4e46b251caa88a872c8d1a1ab61f432b4f813276d1e31e027e60c90a3abd79cd9266689f24956f822a197948491da7ee5da13c0976bf89b5bd433250679c2e91f4d56c6d11c6f8cd70d878bc6af6cf12fb2a191b3c2f5037e233f3648da89570b76418b9fb6afbc6053bd62c0d741fdb946a279c0cd271cd291ca753343646e610bfbdc8860974b52bb00128e852dc153ea67b50aace4261eef54f9a98eb4c091d725c7d4aed8f136e426723a3c2c9ad70431d310b0dc118e86fe8ee566c627d2d1ab463c5782d77aebc37221760535b4d106ef6dc41e89b7557ea75f6525e192d87fb828b5f2d5a71fa8812a1cb7b1054c63343ba2552a93c90e34a0fbf9043593359225cf25df1f67af76989d1ad70d55ef27ab05d56376dfb903332466be419ecd6eece62d16dc2ae7f2dc8c544af9649bb22b1a857880e7134ba824c5d0d0941a81b218edf82294744cac26720ad0ed49d29b1afaed545b5c7da0c33a9a9ace783eb0808c02c8b64723c26fb93cbfe036611f84433004de3c45f13e211fa59e89e8651a170719d1c73d0a2ecaba2b5d3c9b006d77d01f9f37a45ff61a296ed2db282edbe0a10f8a26bfd9d170e4b34ddff8cf08b62356c668580b757899e9dcfbe4dbfaee0c70a9715d6af105591ae59240ed9fae09eaba4b8813866fecf0e1061ee44a43a4ed49658ab8414c8f32e144a52a7b1e7cbfa15fbf9043f87b42c9be8cd1d4d93a00a11a8620945f9dbfe1f75d2ab8ba8009a8e373590640a1cc09fb03b613ddf619880b9b026e333bb0eea39f3bc644c8e0c6ffa8f083efbf369ea496fdbffbe76bbb7aaf9f563d276efa718c416993d7e1ac0b073ff7400d73ed80c2408cc9b3c9b15795c2dcd49581fd39180a606f5c4bcc8ec48b01ef536bf1dd72fe80a69399ac88fbbd01d3af7a9b176a9764bd09a79d41eb3a515ebaa9610393079fbf5ed06d724f37e6cd936d2bd9600c6f0a8588aca88c02061dbb9ab72eeb1809627eb21d8df5c6cf420fa9b6ec0e97d433589669f7a3883a8a980cb0b1f5110f18ddb54f22336c28bafe6f5e7ee2267cbc17c776299a3d04652a984de59eb58b028a25da2549fefa795a51e36f9dece90b5a9e424c42d961b15600ce6d705bdfdada88b056ce0136773d7873ccaba956066320b1610fe67e4833a88baaf3e76c7004db1571112c12b3bf8357f1dc9681a106f7bf8247d8304601b210c820bedcac1d2a8f83fcfe712e03dab18a5107627d1092a054b19e85d57a6707e8fb5be8dd78273afb6897bcdaa17d2a314a2ca1c0436b6e2bb71fc09f4b42561e2bfc92ea188264b117d23712b7b6f23b486c6a477898bb9ca0c4f965cfc17bba797f61f4338689feff81c14562d166439b1a1a0cdf7dfb6543513ac8a86e38a277e6a221a6e1922933b12b7ac7373ce1ad64a0737b68632952c4cbcce5f1cbf458c48ac45ad8fac8ee61f28530f14dc68cb6351bf42e
Plaintext:
In case you want to know why I called this project Midbar - Midbar is a Hebrew word that means "pasture," "uninhabited land," "wilderness," "large tracts of wilderness (around cities)," "desert." I had two reasons for choosing the word Midbar as the name of this project. First - while working on my previous projects, I noticed that the so called "device that keeps your personal data secure in an encrypted form" market is pretty much a "desert around the oasis of the password manager market." Second - I couldn't find a better word to describe that project. At first, I wanted to call it a "Password Vault," but then I realized that it's more than just a password vault. So, I just called it Midbar!
Hash String
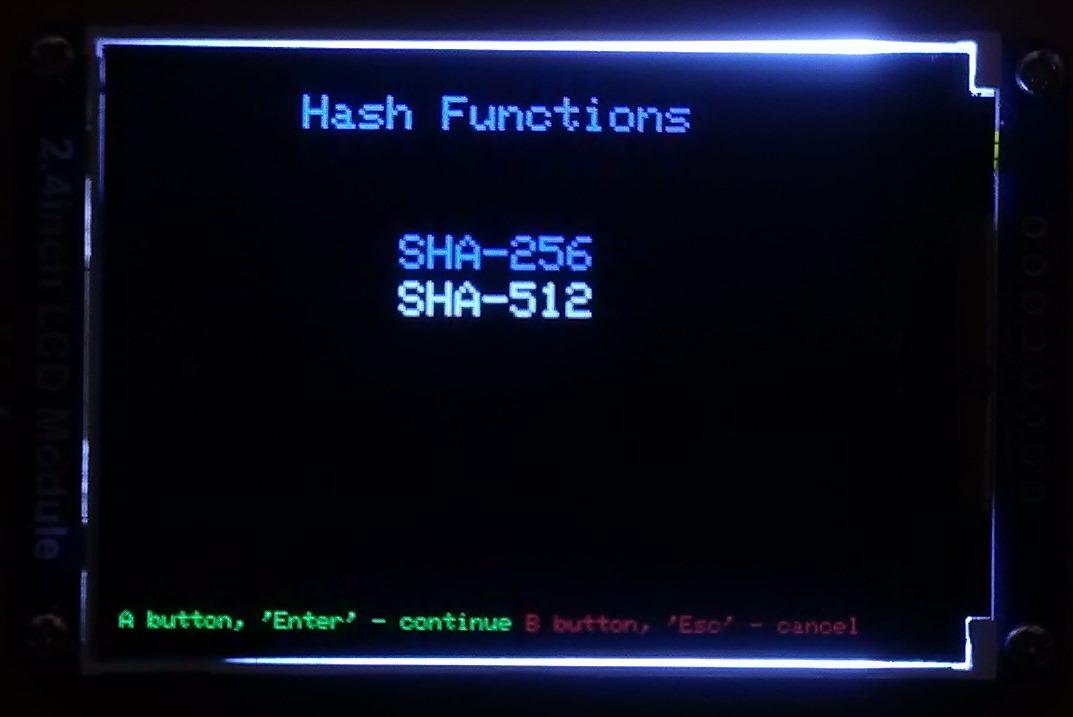
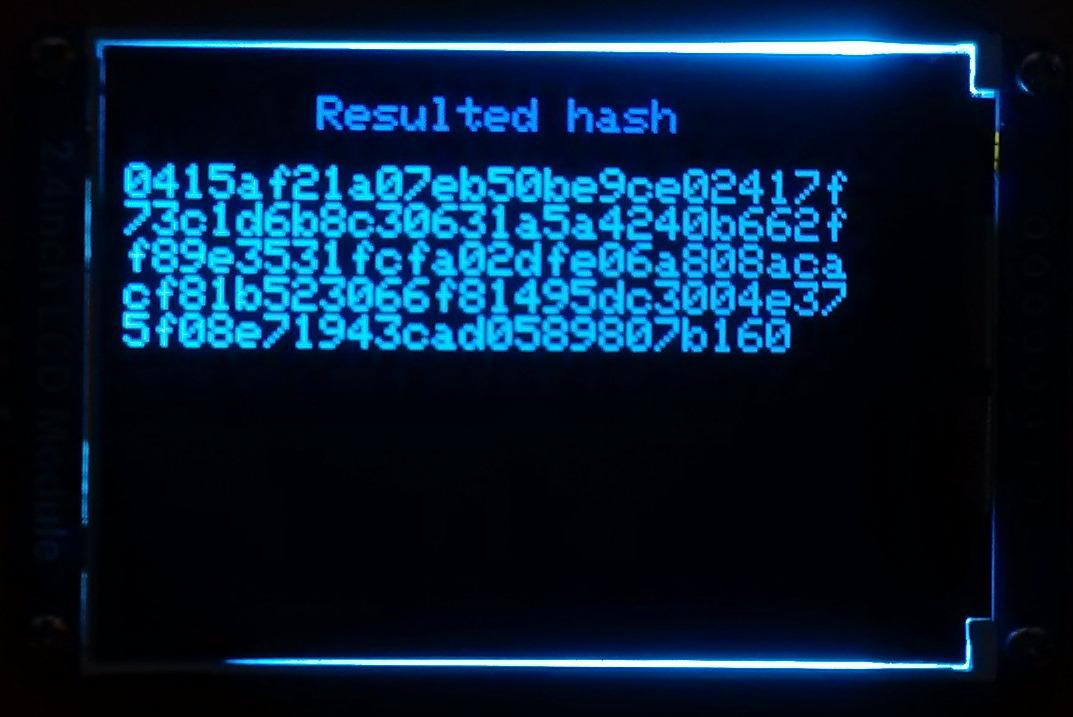
The Midbar utilizes two hash functions: SHA-256 and SHA-512.
If you're not familiar with the hash functions, let me give you a simple explanation of what the hash function is.
The hash function is an algorithm that takes your input (in that case, it's a string) and gives you a fixed-length output derived from that input. One of the essential properties of the hash function is that it always produces the same result for the same input. That allows you to use the hash function to verify the data integrity.
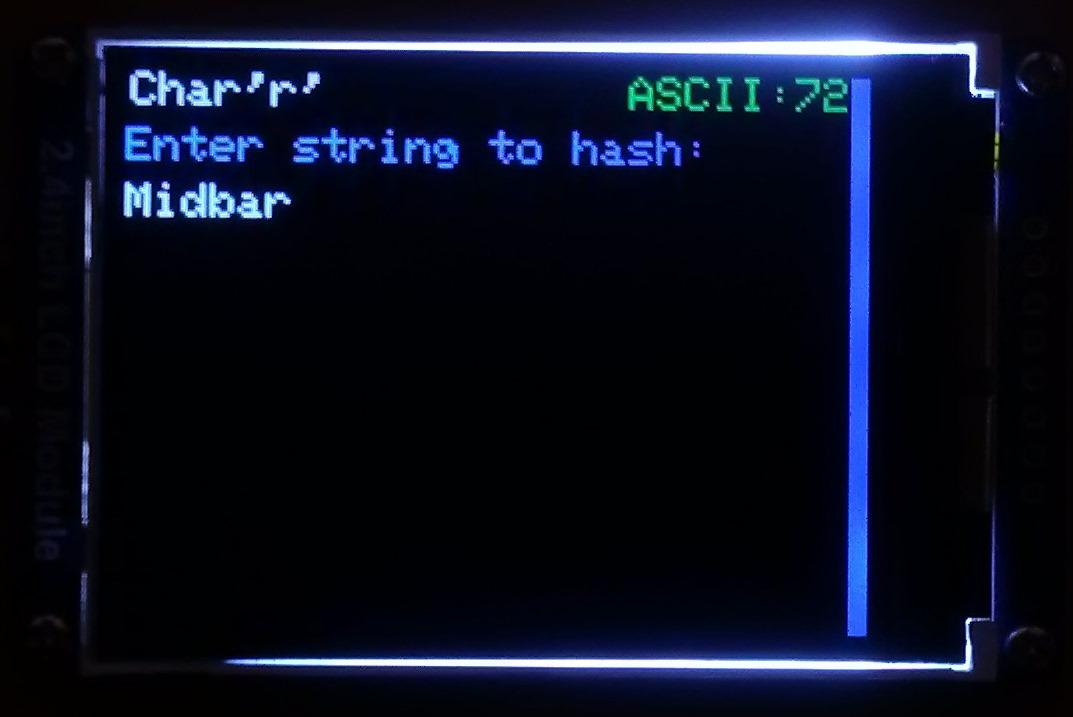
To hash a string:
- Select the "Hash Functions" line in the main menu;
- Either press the "A" button or press the "Enter" key on the PS/2 keyboard;
- Select the "SHA-256" or "SHA-512" line depending on the hash function you'd like to use;
- Either press the "A" button or press the "Enter" key on the PS/2 keyboard;
- Enter the string you'd like to hash;
- Either quad-click the encoder button or press the "Enter" key on the PS/2 keyboard.
Input:
Midbar
Hash:
0415af21a07eb50be9ce02417f73c1d6b8c30631a5a4240b662ff89e3531fcfa02dfe06a808acacf81b523066f81495dc3004e375f08e71943cad0589807b160
Find a Good Use for Midbar
I wouldn't say that this version of Midbar is either (significantly) worse or better than the previous one. I would consider it a branch of Midbar with its own pros and cons.
Although it handles the PS/2 keyboard much better than the previous Midbar and can easily encrypt and decrypt a 10000-character long string without any problems, it has some downsides absent in the Midbar V2.5. It can't execute SQL queries, doesn't have a secure communication channel, and seems to be a bit slower and less stable than the previous Midbar.
But it might turn out that all of these are actually minor issues. Take into account that I'm writing the following based solely on my observations. It seems to me that the Raspberry Pi Pico doesn't have a properly functioning random number generator (or at least I wasn't able to figure out how to work with it). By trying to generate the random values with the "rand()" function, I got a sequence that repeated even after the board was rebooted. I then started googling "how to generate random numbers on Raspberry Pi Pico" and stumbled upon a possible solution. But still, I won't be putting much trust into the Raspberry Pi Pico's RNG.
By the way, let me remind you that the Midbar project isn't there to give you a 100% guarantee for something. It's not about that, and it never was. It's about raising the cost of unauthorized access to your data as high as possible!
And if you want to make your own version of the Midbar or change something in it, please do so! Don't forget that there's always room for improvement, even if it seems that there's none.
That's it for this tutorial.
If you like this tutorial, please share it.
Thank you for reading this tutorial.